TeamPCP Cybercrime Group Targets Iran with Data-Wiping Worm, Leverages Supply Chain Attacks
A financially motivated cybercrime syndicate known as TeamPCP has escalated its operations, unleashing a sophisticated worm designed to infiltrate cloud environments and erase data on systems specifically configured for Iran. This latest offensive, which emerged over the past weekend, marks a significant escalation by the group, which has previously demonstrated a knack for weaponizing exposed cloud infrastructure and exploiting supply chains. The attack highlights the evolving tactics of cybercriminals seeking to exploit geopolitical tensions and exploit vulnerabilities in increasingly complex cloud-native architectures.
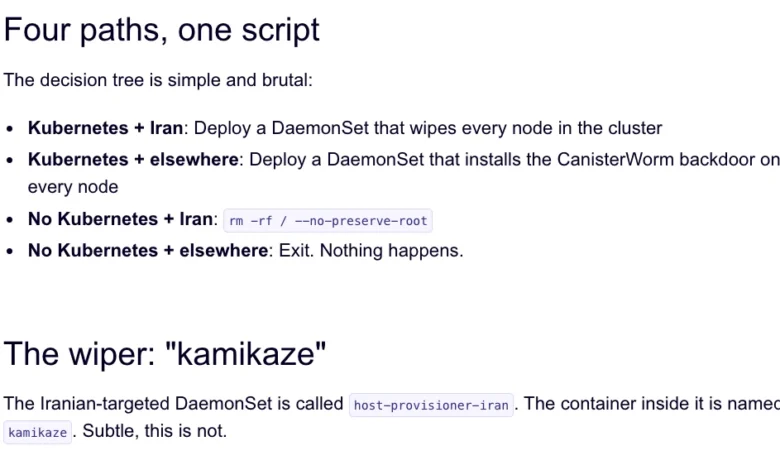
The malicious worm, dubbed "CanisterWorm" by researchers at Aikido, is engineered to identify and destroy data on systems that either use Iran’s standard time zone or have Farsi set as their default language. This targeted approach suggests a deliberate effort to inflict maximum disruption within the Iranian digital landscape. Experts warn that the group’s methodology, which focuses on automated exploitation of misconfigurations rather than novel malware, makes it particularly dangerous and difficult to track.
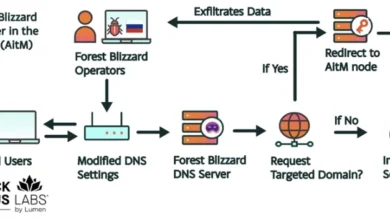
TeamPCP’s Operational Modus Operandi: Industrializing Cloud Exploitation
TeamPCP’s strategy diverges from many traditional cybercrime groups by focusing on the exploitation of cloud control planes rather than individual endpoints. This approach, detailed in a January profile by the cybersecurity firm Flare, targets the underlying infrastructure that manages cloud services. Analysis by Flare indicated that a staggering 97% of TeamPCP’s compromised servers resided on either Microsoft Azure (61%) or Amazon Web Services (AWS) (36%). This heavy reliance on major cloud providers underscores the pervasive nature of cloud security vulnerabilities.
Assaf Morag, a researcher at Flare, characterized TeamPCP’s strength not in the novelty of their exploits, but in the "large-scale automation and integration of well-known attack techniques." He elaborated, "The group industrializes existing vulnerabilities, misconfigurations, and recycled tooling into a cloud-native exploitation platform that turns exposed infrastructure into a self-propagating criminal ecosystem." This industrialization means that TeamPCP can rapidly deploy attacks across a wide range of targets by leveraging pre-existing weaknesses.
A Chronology of Escalation: From Cloud Infiltration to Supply Chain Tampering
TeamPCP’s activity has been meticulously tracked, revealing a pattern of increasingly audacious attacks.
-
December 2023: The group began systematically compromising corporate cloud environments. Their initial vector involved a self-propagating worm that exploited exposed Docker APIs, Kubernetes clusters, Redis servers, and the React2Shell vulnerability. Following initial infiltration, TeamPCP would then attempt to move laterally within victim networks, siphoning authentication credentials. Extortion demands were typically communicated via Telegram.
-
January 2024: Security firm Flare published a detailed profile of TeamPCP, highlighting their focus on cloud infrastructure and their method of "industrializing" existing vulnerabilities. This analysis provided critical insights into the group’s operational strategy.
-
March 19, 2024: TeamPCP executed a significant supply chain attack targeting Trivy, a popular vulnerability scanner developed by Aqua Security. The attackers successfully injected credential-stealing malware into official releases hosted on GitHub Actions. While Aqua Security moved swiftly to remove the malicious files, the security firm Wiz confirmed that attackers had managed to publish compromised versions capable of exfiltrating SSH keys, cloud credentials, Kubernetes tokens, and cryptocurrency wallets from unsuspecting users.
-
Weekend of March 23-24, 2024: The same technical infrastructure used in the Trivy attack was repurposed to deploy the new data-wiping payload targeting Iran. Charlie Eriksen, a security researcher at Aikido, reported that this wiper component is triggered if the victim’s system is identified as belonging to Iran based on its timezone and locale settings.
The "CanisterWorm": A Blockchain-Resistant Command and Control
A key innovation in TeamPCP’s arsenal is their use of the Internet Computer Protocol (ICP) canister, which Aikido refers to as "CanisterWorm." ICP canisters are tamperproof, blockchain-based "smart contracts" that combine code and data. Their distributed architecture makes them highly resistant to takedown attempts, as they can serve web content directly and remain accessible as long as their operators pay the necessary virtual currency fees.
This reliance on ICP canisters for orchestrating their campaigns provides TeamPCP with a degree of operational anonymity and resilience against traditional law enforcement or cybersecurity interventions. The distributed nature of the ICP network means there is no single point of failure to target for disruption.

Bragging Rights and the Threat of Escalation
Evidence suggests that the individuals behind TeamPCP are not only adept at cyber warfare but also eager to boast about their capabilities. They have reportedly been discussing their exploits in a Telegram group, claiming to have pilfered vast quantities of sensitive data from major corporations, including a large multinational pharmaceutical firm.
"When they compromised Aqua a second time, they took a lot of GitHub accounts and started spamming these with junk messages," Eriksen told KrebsOnSecurity. "It was almost like they were just showing off how much access they had. Clearly, they have an entire stash of these credentials, and what we’ve seen so far is probably a small sample of what they have."
This behavior has broader implications for the cybersecurity ecosystem. Security experts like Catalin Cimpanu, in his newsletter "Risky Business," have noted that such spamming of compromised repositories could be a tactic to artificially boost the visibility of malicious code packages in GitHub searches, making them appear more legitimate or popular. This practice, coupled with the use of services that sell GitHub stars and "likes," contributes to a growing problem of malware proliferation on the platform.
Broader Implications: The Perils of Supply Chain Attacks
The attack on Trivy was not an isolated incident. It represented the second major supply chain attack involving the scanner in as many months. In late February, Trivy was targeted by "HackerBot-Claw," an automated threat that exploited misconfigured GitHub Actions workflows to steal authentication tokens.
The fact that TeamPCP appears to have leveraged access gained from the initial compromise of Aqua Security to execute the subsequent wiper attack underscores the cascading risks inherent in supply chain compromises. A single breach in a widely used tool can have far-reaching consequences across numerous organizations that rely on that tool for their security posture.
Uncertainty and the "Chaotic Evil" Persona
Despite the sophisticated nature of TeamPCP’s operations, the actual impact of the Iranian data-wiping worm remains somewhat uncertain. Eriksen noted that the malicious payload was only active for a short period over the weekend and that the group has been rapidly deploying and withdrawing the code, adding new features.
"They’ve been taking [the malicious code] up and down, rapidly changing it adding new features," Eriksen observed. He also pointed out that at times, the malicious canister was redirecting visitors to a Rick Astley "Rick Roll" video on YouTube. This seemingly contradictory behavior, oscillating between targeted destruction and playful trolling, leads Eriksen to speculate about the group’s motivations: "It’s a little all over the place, and there’s a chance this whole Iran thing is just their way of getting attention. I feel like these people are really playing this Chaotic Evil role here."
This apparent "chaotic evil" persona, coupled with their sophisticated technical capabilities, makes TeamPCP a particularly unpredictable and concerning threat actor.
The Growing Challenge for GitHub and Cloud Providers
The increasing frequency and sophistication of supply chain attacks have placed immense pressure on platforms like GitHub and cloud providers. Cimpanu’s analysis highlights that while security firms are making strides in identifying these threats, the onus is also on platforms like GitHub to bolster their defenses.
"While security firms appear to be doing a good job spotting this, we’re also gonna need GitHub’s security team to step up," Cimpanu wrote. "Unfortunately, on a platform designed to copy (fork) a project and create new versions of it (clones), spotting malicious additions to clones of legitimate repos might be quite the engineering problem to fix."
Expanding Reach: KICS Vulnerability Scanner Also Targeted
In an update on March 23rd, Wiz reported that TeamPCP had also infiltrated the GitHub Action for KICS, a security scanner from Checkmarx. This credential-stealing malware was present in the KICS GitHub Action between 12:58 and 16:50 UTC on March 23rd, further broadening the scope of TeamPCP’s supply chain compromises and highlighting their persistent efforts to inject malicious code into critical developer tools.
The ongoing actions of TeamPCP underscore a critical vulnerability in the modern digital ecosystem: the reliance on interconnected software and cloud services. As these systems become more complex and intertwined, the potential for a single actor to inflict widespread damage grows, demanding a more robust and collaborative approach to cybersecurity from both private industry and platform providers. The financial motivations behind TeamPCP suggest that their attacks are likely to continue, evolving as they seek new avenues to exploit and profit.