Grinex Halts Operations Amidst Alleged $13.7 Million Cyberattack, Blames Foreign Intelligence

Kyrgyzstan-incorporated cryptocurrency exchange Grinex, already under sanctions from the United Kingdom and the United States, announced on April 18, 2026, the suspension of its operations. The exchange attributes this drastic measure to a sophisticated cyberattack that it claims resulted in the theft of over 1 billion rubles (approximately $13.74 million) in user funds. Grinex’s statement pointed fingers at "foreign intelligence agencies," alleging the attack bore the hallmarks of state-sponsored actors and was orchestrated to destabilize Russia’s financial sovereignty.
The dramatic announcement comes a year after Grinex, widely believed to be a rebranding of the sanctioned Russian cryptocurrency exchange Garantex, was included in new sanctions lists by both the U.S. and the U.K. The exchange’s leadership asserted that the recent cyber incident represented an "unprecedented level of resources and technological sophistication," capabilities they claim are "typically available exclusively to the agencies of hostile states." This framing suggests a deliberate, politically motivated attack aimed at undermining Russia’s financial infrastructure, particularly in the context of existing international sanctions.
Background: A History of Sanctions and Evasion
Grinex’s operational halt is deeply intertwined with the history of Garantex, its predecessor. Garantex was initially sanctioned by the U.S. Treasury Department in April 2022. The Treasury cited Garantex’s role in laundering funds linked to ransomware attacks and illicit activities on darknet markets such as Conti and Hydra. This initial action signaled a growing international effort to curb the use of cryptocurrencies for illicit finance and sanctions evasion.
The U.S. Treasury further tightened the noose on Garantex in August 2025, renewing sanctions after the exchange was found to have processed over $100 million in illicit transactions. Investigations by blockchain intelligence firms Elliptic and TRM Labs revealed that Garantex had, in response to these sanctions, shifted its customer base to Grinex, operating under a new guise. This strategic pivot allowed the exchange to continue its operations, reportedly by leveraging a ruble-backed stablecoin known as A7A5, a method that provided a degree of anonymity and facilitated continued transactions within a restricted ecosystem.
The Alleged Cyberattack: A Detailed Chronology
The alleged cyberattack on Grinex, and a simultaneous smaller incident at a related exchange, unfolded rapidly in mid-April 2026. According to reports from blockchain analytics firm Elliptic, the primary asset theft occurred on April 15, 2026, around 12:00 UTC. The attackers reportedly targeted Grinex, siphoning user funds totaling over 1 billion rubles.
The stolen assets, primarily Tether (USDT) stablecoins, were then quickly moved to other accounts on the TRON and Ethereum blockchains. Elliptic’s analysis highlighted a critical evasion tactic: the immediate conversion of USDT to either TRON (TRX) or Ether (ETH). This maneuver is designed to circumvent potential freezing of the USDT by Tether, the issuer of the stablecoin, which often cooperates with law enforcement and regulatory bodies to block illicit funds.

On the same day as the Grinex breach, TokenSpot, a Kyrgyzstan-based exchange identified by TRM Labs as likely operating as a front for Grinex, also experienced disruptions. TokenSpot posted a notification on its Telegram channel on April 15, 2026, stating that its platform would be temporarily unavailable due to technical maintenance. The following day, April 16, 2026, TokenSpot announced the resumption of full operations. While TokenSpot was impacted, the estimated loss from this secondary incident was significantly smaller, reportedly less than $5,000. Intriguingly, the funds stolen from TokenSpot were routed through two of its addresses to the same consolidation address that received funds from the Grinex-linked wallets, further suggesting a coordinated or connected operation.
TRM Labs identified approximately 70 blockchain addresses associated with the Grinex incident, underscoring the scale and complexity of the alleged attack.
Analytical Insights into the Attack’s Methodology
Blockchain intelligence firms have provided detailed insights into the modus operandi of the alleged attackers. Chainalysis, in its analysis, confirmed the rapid swapping of stablecoin funds for non-freezable tokens. This "frantic swapping" strategy is a recognized tactic employed by malicious actors seeking to launder their illicit proceeds before authorities or stablecoin issuers can intervene and freeze the assets. By converting the stolen USDT into more decentralized cryptocurrencies like TRX or ETH, the attackers aimed to create a more challenging trail for forensic investigators.
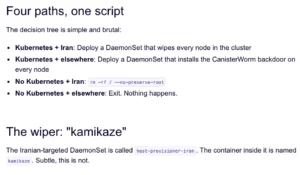
The sophistication of the attack, as described by Grinex, coupled with the evasion techniques observed on-chain, has led to speculation about the true nature of the incident. Chainalysis raised the possibility of a "false flag attack." Given Grinex’s heavily sanctioned status and its limited operational ecosystem, the firm suggested that the incident might not be a straightforward exploit by external cybercriminals but could potentially be an orchestrated event by insiders or entities with ties to Russia. The rationale behind such a false flag operation could be to deflect scrutiny from legitimate sanctions evasion activities or to create a narrative that portrays Russian financial entities as victims of foreign aggression rather than perpetrators of illicit finance.
Grinex’s Statement and Accusations
Grinex’s official statement, posted on its website, was unequivocal in its accusations. "Digital forensic evidence and the nature of the attack point to an unprecedented level of resources and technological sophistication – capabilities typically available exclusively to the agencies of hostile states," the company declared. This language directly implicates state actors and frames the attack as an act of cyber warfare against Russia’s financial infrastructure.
A spokesperson for Grinex further elaborated, stating that the exchange’s infrastructure had been under continuous attack since its inception. However, they characterized the latest event as a "new level of escalation" specifically aimed at "destabilizing the domestic financial sector." This narrative aligns with the broader geopolitical context and the ongoing efforts to isolate Russia economically through sanctions.
Broader Implications for Sanctions Evasion and Regulatory Compliance
The Grinex incident, regardless of its true origins, has significant implications for the global fight against money laundering and sanctions evasion. The exchange’s ability to operate for an extended period despite being sanctioned by major global powers highlights the persistent challenges in effectively enforcing financial restrictions in the rapidly evolving cryptocurrency landscape.

The use of rebrands, stablecoins, and cross-chain transactions to obscure the movement of illicit funds demonstrates the adaptability of entities seeking to circumvent regulatory oversight. The involvement of exchanges like Grinex and Rapira (another Georgia-incorporated exchange with a Moscow office that reportedly conducted over $72 million in direct cryptoasset transactions with Grinex, according to Elliptic) underscores a pattern of Russian-linked cryptocurrency services facilitating sanctions evasion.
The disruption of Grinex, whether a genuine hack or a false flag operation, undoubtedly deals a blow to the infrastructure that supports such evasion tactics. However, the incident also serves as a stark reminder of the need for enhanced international cooperation, more robust regulatory frameworks for digital assets, and improved on-chain and off-chain intelligence gathering to counter these sophisticated financial crimes.
Reactions from Related Parties (Inferred)
While official statements from governments or international regulatory bodies directly addressing the Grinex hack incident were not immediately available at the time of reporting, their past actions provide context. The U.S. Treasury Department and the U.K.’s Office of Financial Sanctions Implementation (OFSI) have consistently targeted entities involved in facilitating illicit finance and sanctions evasion. Their continued inclusion of Garantex and Grinex on sanctions lists indicates a sustained commitment to disrupting these activities.
Blockchain intelligence firms like Elliptic, TRM Labs, and Chainalysis play a crucial role in providing the data and analysis that underpin these enforcement actions. Their detailed reports and findings are instrumental in tracing illicit fund flows and identifying the actors involved. The public sharing of their analytical insights in relation to the Grinex incident serves to inform the broader cybersecurity and financial crime communities about the evolving tactics used in sanctions evasion.
The operational halt of Grinex, while framed by the exchange as an act of victimhood, effectively removes a known node in the network used for circumventing international financial restrictions. This outcome, regardless of the cause, aligns with the objectives of sanctions regimes aimed at isolating and pressuring targeted economies. The industry will be watching closely to see if this event leads to further investigations and potentially more targeted actions against entities and individuals involved in the cryptocurrency space with ties to sanctioned jurisdictions.