Russian Military Intelligence Exploits Unpatched Routers to Harvest Microsoft Office Authentication Tokens
Hackers associated with Russia’s military intelligence units have been systematically exploiting well-known vulnerabilities in older Internet routers to mass harvest authentication tokens from Microsoft Office users. This sophisticated and stealthy espionage campaign, detailed by security experts today, allowed state-backed Russian threat actors to exfiltrate sensitive authentication data from over 18,000 networks without deploying any traditional malicious software or code.
Microsoft, in a detailed blog post released on April 7, 2026, revealed that it had identified more than 200 organizations and approximately 5,000 consumer devices compromised by a covert yet remarkably simple spying operation. This network was orchestrated by a Russia-backed threat actor known in cybersecurity circles as "Forest Blizzard." The group’s operational methods have raised significant concerns among cybersecurity professionals and government agencies worldwide, highlighting a persistent and evolving threat landscape.
Forest Blizzard: A Persistent Threat Actor with a History
Forest Blizzard is widely recognized within the intelligence community under multiple aliases, including APT28 and Fancy Bear. These designations are attributed to military intelligence units operating under the purview of Russia’s General Staff Main Intelligence Directorate (GRU). The group’s notoriety was cemented in 2016 when it famously infiltrated the campaign of Hillary Clinton, the Democratic National Committee (DNC), and the Democratic Congressional Campaign Committee (DCCC). These breaches were part of a concerted effort to interfere with the U.S. presidential election, underscoring the group’s history of targeting sensitive political and governmental entities.
The current operation, uncovered by researchers at Black Lotus Labs, the security division of global Internet backbone provider Lumen, paints a picture of a highly effective and resource-efficient cyber-espionage campaign. At the apex of its activity in December 2025, Forest Blizzard’s surveillance network had successfully ensnared more than 18,000 Internet routers. Crucially, these compromised devices were predominantly older, end-of-life models or routers that had not received critical security updates for extended periods.
A comprehensive report published by Lumen details that the primary targets of this campaign were government agencies, including ministries of foreign affairs, law enforcement bodies, and third-party email providers. This strategic targeting suggests an objective to gain access to sensitive diplomatic, intelligence, and operational data.
The Ingenious Exploitation of DNS Hijacking
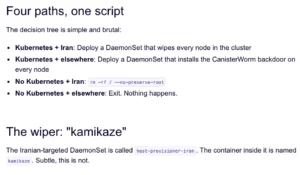
Ryan English, a security engineer at Black Lotus Labs, elaborated on the technical sophistication of the GRU hackers’ approach. He emphasized that the attackers did not need to install any malware on the targeted routers, which were predominantly older Mikrotik and TP-Link devices commonly found in Small Office/Home Office (SOHO) environments. Instead, the hackers leveraged well-documented, pre-existing vulnerabilities within these routers.
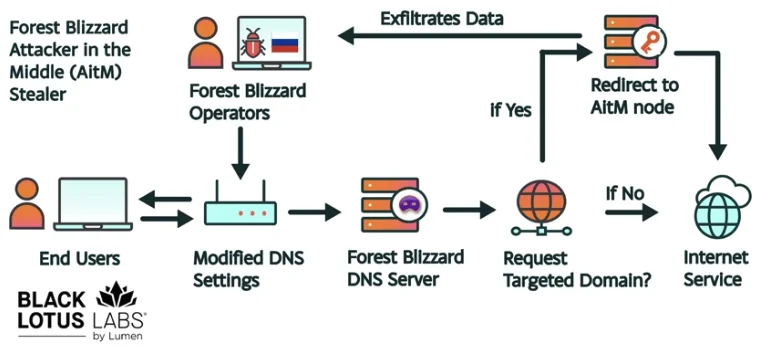
The core of the attack involved modifying the Domain Name System (DNS) settings of the routers. By exploiting these flaws, the attackers were able to redirect DNS requests to servers under their direct control. DNS is the fundamental infrastructure that translates human-readable website addresses (like www.example.com) into the numerical IP addresses that computers use to locate resources on the internet.
The U.K.’s National Cyber Security Centre (NCSC), in a new advisory that corroborates the findings regarding Russian cyber actors compromising routers, further explained the implications of DNS hijacking. This attack vector allows malicious actors to intercept and manipulate the DNS resolution process. Consequently, users attempting to access legitimate websites can be silently redirected to fraudulent, malicious sites designed to mimic the originals. These fake sites are often used to harvest login credentials, personal information, or other sensitive data.
English further clarified that the routers compromised by Forest Blizzard were reconfigured to utilize DNS servers that pointed to a small cluster of virtual private servers (VPS) operated by the attackers. This seemingly simple alteration had profound consequences. The compromised routers, acting as gateways for local networks, could then propagate these malicious DNS settings to all connected users. From this point forward, any authentication tokens transmitted by these users, particularly those related to Microsoft Office applications and services, could be intercepted.
Bypassing Multi-Factor Authentication: The Critical Impact of Token Harvesting
A particularly alarming aspect of Forest Blizzard’s operation is its ability to bypass robust security measures like multi-factor authentication (MFA). Authentication tokens, often generated after a user has successfully logged in and completed MFA challenges, represent a highly privileged form of access. These tokens are typically valid for a limited time and grant access to resources without requiring repeated authentication.

By intercepting these tokens, the attackers could gain direct, unauthorized access to victim accounts. This bypasses the need to phish for individual user credentials or one-time codes, a more labor-intensive and often detectable method. The sophistication lies in targeting the point after a user has already been verified by multiple security layers.
"Everyone is looking for some sophisticated malware to drop something on your mobile devices or something," English commented, highlighting the conventional focus of cybersecurity efforts. "These guys didn’t use malware. They did this in an old-school, graybeard way that isn’t really sexy but it gets the job done." This sentiment underscores a critical shift in threat actor methodologies, favoring exploitation of fundamental infrastructure weaknesses over complex malware development.
Microsoft describes Forest Blizzard’s activities as employing DNS hijacking to facilitate "post-compromise adversary-in-the-middle (AiTM) attacks on Transport Layer Security (TLS) connections against Microsoft Outlook on the web domains." While the targeting of SOHO devices is not a novel tactic, Microsoft noted this is the first instance where Forest Blizzard has utilized "DNS hijacking at scale to support AiTM of TLS connections after exploiting edge devices." This marks a significant escalation in the group’s operational capabilities and ambition.
A Pattern of Adaptation: Forest Blizzard’s Evolving Tactics
Danny Adamitis, another engineer at Black Lotus Labs, suggested that it will be instructive to observe Forest Blizzard’s response to the increased attention their espionage operation has garnered. He pointed to a precedent set in August 2025, when a similar NCSC report detailing APT28’s router exploitation tactics prompted a swift shift in the group’s methods.
Prior to that NCSC report, Forest Blizzard had employed malware to control a more narrowly defined and smaller set of compromised routers. However, the day following the NCSC’s advisory, the group rapidly abandoned its malware-centric approach. Instead, it transitioned to the mass alteration of DNS settings on thousands of vulnerable routers, a tactic that proved far more scalable and impactful.
"Before the last NCSC report came out they used this capability in very limited instances," Adamitis stated. "After the report was released they implemented the capability in a more systemic fashion and used it to target everything that was vulnerable." This demonstrates a pattern of adaptation and learning by the threat actor, where public disclosures of their methods lead to a rapid evolution of their attack vectors to maintain operational effectiveness.
Regulatory Responses and Broader Security Implications
The vulnerabilities exploited by Forest Blizzard are not unique to a single router manufacturer. TP-Link, a prominent router maker, has previously faced scrutiny, including proposals for a complete ban in the United States. However, the issue of foreign-made, potentially insecure routers has prompted a broader regulatory response.
On March 23, 2026, the U.S. Federal Communications Commission (FCC) announced a significant policy shift. The commission declared that it would no longer certify consumer-grade Internet routers manufactured outside of the United States. This decision reflects a growing concern within U.S. government circles about the national security risks posed by foreign-produced networking equipment.
The FCC explicitly warned that poorly secured routers present "a severe cybersecurity risk that could be leveraged to immediately and severely disrupt U.S. critical infrastructure and directly harm U.S. persons." This statement underscores the potential for such vulnerabilities to be weaponized in state-sponsored cyberattacks.
While the FCC’s new policy aims to bolster national security, experts have raised practical concerns. It is anticipated that few new consumer-grade routers will be available for purchase under this new policy, with potential exceptions like Starlink satellite internet routers produced domestically. The FCC has indicated that router manufacturers can apply for a "conditional approval" from the Department of War or Department of Homeland Security. Importantly, the new policy does not retroactively affect routers already purchased by consumers.
The Forest Blizzard operation serves as a stark reminder of the persistent threat posed by sophisticated nation-state actors and the critical importance of maintaining up-to-date security on all network infrastructure. The exploitation of unpatched routers, a foundational element of internet connectivity for millions, highlights a critical gap in cybersecurity defenses that threat actors are increasingly adept at exploiting. The ongoing evolution of these tactics necessitates a proactive and adaptive approach from both cybersecurity professionals and end-users to safeguard digital assets and maintain the integrity of global communication networks. The focus on exploiting fundamental infrastructure weaknesses rather than complex malware suggests a strategic shift towards more resilient and harder-to-detect attack methodologies.