Ghost Identities: The Unseen Threat Dominating Cloud Breaches, Leaving Organizations Vulnerable
The escalating sophistication of cyber threats has shifted the focus from traditional human-centric attacks to a more insidious danger lurking within the digital infrastructure of businesses: unmanaged non-human identities. In 2024, a staggering 68% of cloud breaches were attributed not to phishing or weak passwords, but to compromised service accounts and forgotten API keys – the digital "keys" left carelessly lying around. This alarming statistic underscores a critical vulnerability in enterprise security, one that traditional identity and access management (IAM) systems are ill-equipped to handle.
The exponential growth of cloud adoption and the increasing reliance on automation, artificial intelligence, and interconnected services have led to a proliferation of automated credentials. For every human employee within an organization, there are an estimated 40 to 50 automated identities, including service accounts, API tokens, AI agent connections, and OAuth grants. These digital entities, designed to facilitate seamless operations and inter-application communication, often persist long after their initial purpose has been served. Projects conclude, employees depart, and yet these fully privileged, unmonitored credentials remain active, creating vast attack surfaces.
The Silent Attackers: Exploiting the Shadow Workforce
Cybercriminals are increasingly recognizing the value of these "ghost identities." Instead of expending resources to crack complex human passwords or bypass sophisticated phishing defenses, attackers can simply identify and exploit these dormant, powerful credentials. The analogy of leaving the back door unlocked is particularly apt; these automated identities represent a direct pathway into an organization’s most sensitive data and critical systems.
The problem is compounded by the rapid evolution of technology. AI agents and automated workflows are generating these machine identities at an unprecedented pace, far exceeding the capacity of human security teams to manually track and manage them. Many of these identities are granted excessive permissions, often carrying administrative-level access they never truly required for their specific functions. This over-provisioning of privileges transforms a minor security oversight into a catastrophic breach waiting to happen. A single compromised token can grant an attacker the freedom to move laterally across an entire environment, establishing a foothold that can remain undetected for extended periods. Industry data indicates an average dwell time for such intrusions exceeding 200 days, allowing attackers ample opportunity to exfiltrate data, disrupt operations, or embed themselves deeper within the network.
The Limitations of Traditional IAM
The foundational principles of traditional Identity and Access Management (IAM) were designed for a human-centric world. These systems excel at managing user accounts, authenticating employees, and enforcing access policies for individuals. However, they largely overlook the burgeoning realm of machine-to-machine interactions and automated processes. Consequently, the vast ecosystem of service accounts, API keys, and other non-human identities often falls outside the purview of conventional security controls, creating a significant blind spot.
This disconnect leaves organizations exposed to a novel class of threats that bypass established security perimeters. The very tools and technologies designed to enhance efficiency and innovation are inadvertently becoming vectors for compromise.
A Growing Threat Landscape: Data and Projections
While specific anonymized data points for 2024 cloud breaches attributed to non-human identities are emerging, the trend has been building for years. Reports from cybersecurity firms have consistently highlighted the growing role of compromised credentials in breaches. For instance, a 2023 analysis by Verizon indicated that stolen or compromised credentials were a factor in a significant percentage of data breaches across various industries. The extrapolation of these trends suggests that the 68% figure for 2024 is not an anomaly but a stark reflection of an evolving threat landscape.
The proliferation of cloud-native architectures, microservices, and DevOps practices further exacerbates this issue. Each new service deployed, each new integration established, potentially introduces new machine identities that require careful management. The complexity inherent in modern IT environments means that manual oversight is becoming increasingly untenable.
The Rise of "Ghost Identities": A Deeper Dive
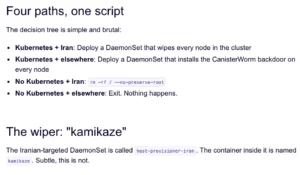
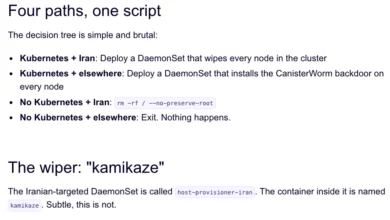
The term "Ghost Identities" aptly describes these forgotten or unmanaged automated credentials. They are the spectral remnants of past operations, lingering in the digital ether with significant power. These identities can include:
![[Webinar] Eliminate Ghost Identities Before They Expose Your Enterprise Data](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEi6vJpO9kksCQDpSksNkqDFNUCbXD70dMGYqI6P9S_XPMY5d8BR8PVdrsVQP1ZJO_-nzL6eQShM3Cap9heQ5kAglsPjfxwIcXPSsf_cfgUVnGQ2XzIWVOuo7JhxMjnHYDN6r9KlQ6LqZJisRZkjatnWChuzUkSlXRa1hFseUPq28PZ5gjGR7L2WzTFdZ3fM/s1700-e365/ghost.jpg)
- Service Accounts: Used by applications and services to authenticate with other services, often with elevated privileges.
- API Keys: Provide programmatic access to cloud services and applications. If compromised, they can grant attackers the ability to manipulate data or resources.
- AI Agent Connections: As organizations deploy more AI-powered tools and agents, these entities require credentials to interact with data and systems, often with broad access.
- OAuth Grants: Allow third-party applications to access user data or perform actions on behalf of a user without needing their direct credentials. Improperly managed grants can be exploited.
- Managed Identities in Cloud Platforms: While designed for security, misconfigurations or over-provisioning can still lead to vulnerabilities.
The critical issue is not the existence of these identities but their lack of continuous monitoring, auditing, and lifecycle management. When an employee leaves, their human account is typically deactivated. However, the service accounts and API keys they may have used or created often persist, retaining their access privileges indefinitely.
Implications for Enterprise Security
The implications of unmanaged ghost identities are far-reaching and severe:
- Increased Attack Surface: Every unmonitored credential represents an open door for attackers.
- Lateral Movement: Compromised machine identities provide a swift and efficient means for attackers to move throughout an organization’s network, escalating their privileges.
- Data Exfiltration and Manipulation: Attackers can leverage these identities to access, steal, or alter sensitive data.
- Service Disruption: Malicious actors can use compromised credentials to disrupt critical business operations.
- Compliance Violations: The presence of unsecured, privileged credentials can lead to significant compliance failures and hefty fines.
- Extended Dwell Time: The stealthy nature of these attacks means organizations may not discover a breach for months, allowing attackers to cause maximum damage.
Towards a Solution: Proactive Management and Emerging Technologies
Addressing the ghost identity threat requires a fundamental shift in how organizations approach identity and access management. Traditional IAM solutions, focused on human users, are insufficient. The industry is increasingly recognizing the need for specialized solutions that can:
- Discover and Inventory: Automatically identify all machine identities across cloud environments, applications, and services.
- Monitor and Audit: Continuously track the activity of these identities, detecting anomalous behavior.
- Enforce Least Privilege: Ensure that each machine identity has only the minimum necessary permissions to perform its function.
- Automate Lifecycle Management: Implement processes for provisioning, de-provisioning, and regular credential rotation.
- Integrate with Security Workflows: Feed insights about machine identities into broader security information and event management (SIEM) and security orchestration, automation, and response (SOAR) platforms.
A Call to Action: Webinar Offers a Playbook for Defense
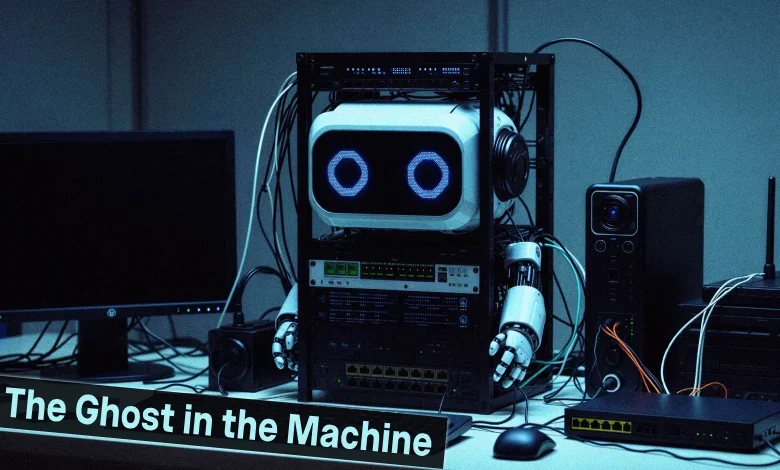
Recognizing the urgency of this issue, The Hacker News is hosting an upcoming webinar titled "Ghost in the Machine." This session aims to provide a practical, actionable guide for security teams to tackle the pervasive threat of unmanaged non-human identities. The webinar will not be a product demonstration but a working playbook, offering strategies and techniques that can be implemented immediately.
The session will guide participants through the process of:
- Identifying the scope of the problem within their organization.
- Discovering dormant and over-privileged machine identities.
- Implementing robust policies for credential management.
- Leveraging automation to maintain security hygiene.
Attendees will gain insights into how to secure these often-overlooked identities, thereby fortifying their defenses against a growing wave of sophisticated cyberattacks. The emphasis is on providing tangible, take-away strategies that can be applied to secure the increasingly complex digital infrastructure of modern enterprises.
Broader Impact and the Future of Enterprise Security
The rise of ghost identities is indicative of a larger trend: the blurring lines between human and machine interaction in the digital realm. As AI and automation become more integral to business operations, the security paradigm must adapt. The focus will increasingly shift from solely protecting human users to securing the entire ecosystem of identities, both human and non-human.
Organizations that fail to address this challenge risk becoming increasingly vulnerable to breaches that can have devastating financial, reputational, and operational consequences. Proactive identification, management, and security of machine identities are no longer optional but a critical imperative for maintaining a robust and resilient enterprise security posture in the age of intelligent automation.
Registering for the "Ghost in the Machine" webinar offers a timely opportunity for organizations to equip themselves with the knowledge and tools necessary to navigate this evolving threat landscape and safeguard their digital assets against the unseen dangers lurking within their own systems.