Massive "0ktapus" Phishing Campaign Compromises Over 9,900 Accounts at 130+ Organizations by Exploiting Multi-Factor Authentication

A sophisticated and widespread phishing campaign, dubbed "0ktapus" by cybersecurity researchers, has ensnared over 130 organizations globally, leading to the compromise of more than 9,900 accounts. The attackers’ primary objective was to steal Okta identity credentials and multi-factor authentication (MFA) codes, leveraging a tactic that effectively bypassed commonly implemented security measures. The breadth of this operation, which has targeted prominent companies like Twilio and Cloudflare, underscores a significant vulnerability in how many businesses implement and educate their employees about MFA.
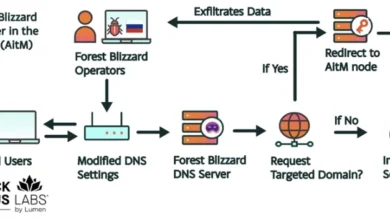
The 0ktapus campaign, meticulously detailed in a recent report by Group-IB, utilized a deceptive strategy of sending text messages containing links to phishing websites that expertly mimicked the Okta authentication pages of targeted organizations. Employees, accustomed to using Okta for secure access, were tricked into entering their usernames, passwords, and crucially, their MFA codes, thereby granting attackers unfettered access to their accounts. The report highlights that the primary goal of the threat actors was to obtain Okta identity credentials and multi-factor authentication (MFA) codes from users of the targeted organizations. These users received text messages containing links to phishing sites that mimicked the Okta authentication page of their organization.
The scale of the breach is staggering, with 114 US-based firms falling victim to this campaign, alongside victims scattered across 68 other countries. Roberto Martinez, senior threat intelligence analyst at Group-IB, emphasized the ongoing nature of the investigation and the potential for the full impact to remain unknown for some time. "The 0ktapus campaign has been incredibly successful, and the full scale of it may not be known for some time," Martinez stated, indicating that the current figures might only represent a fraction of the total damage.
The Genesis of the 0ktapus Operation
The initial phase of the 0ktapus campaign appears to have involved a calculated approach to gather essential intelligence for subsequent attacks. Researchers hypothesize that the threat actors began by targeting telecommunications companies. This strategic move would have provided them with a crucial asset: a comprehensive list of phone numbers. While the exact methodology for obtaining these numbers remains under investigation, one prevailing theory suggests that initial compromises of mobile operators and telecommunications companies allowed the attackers to amass the phone numbers subsequently used in the MFA-related attacks.
With a database of targeted phone numbers in hand, the attackers moved to the next phase: delivering their phishing payload. Text messages, a familiar and often trusted communication channel, were employed to deliver links to the fraudulent Okta login pages. The sophistication of these fake pages, designed to perfectly replicate legitimate Okta interfaces, made them highly convincing to unsuspecting employees. Once a user entered their Okta credentials and MFA code, the attackers gained immediate access.
Group-IB’s technical analysis further elaborates that the initial compromises of software-as-a-service (SaaS) firms were a deliberate "phase-one" of a multi-pronged attack strategy. The ultimate objective, according to researchers, was to infiltrate company mailing lists or customer-facing systems. This access would then serve as a springboard for more extensive and potentially devastating supply-chain attacks, where the compromise of one entity leads to the compromise of many others within its network or ecosystem.
The DoorDash Incident: A Stark Illustration of 0ktapus Tactics
The potential ramifications of the 0ktapus campaign were starkly illustrated shortly after Group-IB published its findings. The popular food delivery service, DoorDash, revealed it had been the victim of an attack exhibiting all the hallmarks of the 0ktapus operation. In a public statement, DoorDash disclosed that an unauthorized party had exploited stolen credentials belonging to vendor employees to gain access to some of their internal tools.
The consequences for DoorDash were significant. The attackers proceeded to exfiltrate personal information from customers and delivery personnel, including names, phone numbers, email addresses, and delivery addresses. This incident underscores the cascading impact of a successful phishing attack, extending beyond direct employee accounts to encompass sensitive customer data. Group-IB reported that in the course of its campaign, the attacker compromised 5,441 MFA codes, highlighting the sheer volume of credentials being stolen.
The Vulnerability of MFA and the Path Forward
The success of the 0ktapus campaign has brought into sharp focus the inherent vulnerabilities that can exist even within multi-factor authentication systems. While MFA is widely considered a critical security layer, the 0ktapus operation demonstrates that it is not an infallible shield. "Security measures such as MFA can appear secure… but it is clear that attackers can overcome them with relatively simple tools," the Group-IB researchers noted.
This sentiment was echoed by Roger Grimes, data-driven defense evangelist at KnowBe4, who stated, "This is yet another phishing attack showing how easy it is for adversaries to bypass supposedly secure multifactor authentication. It simply does no good to move users from easily phish-able passwords to easily phish-able MFA. It’s a lot of hard work, resources, time, and money, not to get any benefit." Grimes’s statement points to a critical gap in security strategies: the assumption that implementing MFA automatically guarantees robust security without commensurate user education and advanced threat mitigation.
The attackers’ ability to phish MFA codes is often attributed to social engineering tactics that exploit user trust and urgency. By impersonating legitimate services and leveraging common communication channels like SMS, they create scenarios where users are more likely to bypass their usual security vigilance.
Mitigating the Threat: Recommendations and Best Practices
In response to the growing threat posed by campaigns like 0ktapus, cybersecurity experts are advocating for a multi-layered approach to defense. Group-IB researchers have recommended enhanced hygiene practices concerning URLs and password management. Crucially, they emphasize the adoption of more robust MFA solutions, such as FIDO2-compliant security keys. These hardware-based keys offer a higher level of security by requiring a physical presence and are generally more resistant to phishing attacks than software-based token or SMS-based MFA.
Furthermore, Grimes stressed the paramount importance of user education. "Whatever MFA someone uses, the user should be taught about the common types of attacks that are committed against their form of MFA, how to recognize those attacks, and how to respond. We do the same when we tell users to pick passwords but don’t when we tell them to use supposedly more secure MFA," he advised. This highlights a critical deficiency in current security training programs, which often fail to adequately prepare employees for the nuanced threats targeting their MFA implementations.
The 0ktapus campaign serves as a potent reminder that cybersecurity is a dynamic and evolving landscape. As threat actors develop increasingly sophisticated methods, organizations must continuously adapt their defenses, invest in advanced security technologies, and, most importantly, empower their employees with the knowledge and tools to identify and resist these evolving threats. The compromise of over 9,900 accounts is not merely a statistic; it represents a significant breach of trust and a stark warning about the persistent ingenuity of cyber adversaries. The long-term implications of such widespread credential compromise could include identity theft, financial fraud, and further exploitation through supply-chain attacks, demanding a vigilant and proactive response from the global cybersecurity community.