Cal.com Transitions to Closed-Source Development Model Following Rise of AI-Powered Vulnerability Exploitation
Cal.com, the prominent open-source scheduling platform and primary competitor to the proprietary service Calendly, has officially announced its transition to a closed-source development model. This strategic pivot, revealed by the company’s leadership, marks the end of a five-year era during which the project was championed as a hallmark of transparency and community-driven development in the productivity software space. The decision is primarily attributed to the evolving cybersecurity landscape, specifically the emergence of artificial intelligence (AI) tools capable of autonomously identifying and weaponizing software vulnerabilities within public code repositories. This move has sparked a wider debate within the technology sector regarding the long-term viability of the open-source model in an age where AI-augmented cyberattacks are becoming increasingly sophisticated and accessible.
The announcement was spearheaded by Bailey Pumfleet, co-founder of Cal.com, who provided a detailed rationale for the shift in a public address. Pumfleet argued that the traditional advantages of open-source software—namely, the "many eyes" theory of security—are being systematically undermined by the speed and efficiency of modern AI. Historically, identifying a zero-day vulnerability or a complex logic flaw in a large codebase required significant human expertise, time, and manual auditing. However, the advent of Large Language Models (LLMs) and specialized AI security scanners has compressed this timeline from weeks or months to mere hours. According to Pumfleet, the ability of AI to ingest an entire public repository and generate working exploits has fundamentally altered the risk-reward ratio for maintaining an open-source enterprise application.
To support this claim, Pumfleet referenced recent developments in the cybersecurity community where AI models have demonstrated unprecedented capabilities in bug hunting. A notable instance cited involved Claude Mythos, a variant of Anthropic’s Claude model, which was used to identify a 27-year-old vulnerability within the OpenBSD kernel. While that specific bug was responsibly disclosed and patched, it served as a proof-of-concept for how legacy codebases—previously thought to be "battle-hardened" through decades of public exposure—can be dismantled by automated intelligence. For a company like Cal.com, which handles sensitive scheduling data, calendar integrations, and personal information for high-profile clients, the threat of an AI-discovered exploit being used in the wild before a patch can be developed was deemed an unacceptable business risk.
The transition to a closed-source model was not an overnight decision but rather the culmination of an internal divergence that had been underway for some time. Company officials revealed that the production codebase used to power the Cal.com hosted service had already begun to "drift" significantly from the publicly available repository on GitHub. Critical infrastructure components, including authentication protocols, data handling layers, and enterprise-grade security features, had undergone extensive rewrites that were never pushed to the open-source branch. This architectural separation meant that the version the community was auditing was no longer reflective of the software actually being deployed to protect user data. By closing the source officially, Cal.com is aligning its public-facing identity with its internal development practices, effectively ending the pretense of being a fully open-source entity.
The tech industry’s reaction to the move has been polarized, reflecting a deep-seated tension between security advocates and open-source purists. Critics of the decision argue that closing the source code is a regression toward "security through obscurity," a practice generally discouraged by cybersecurity experts. The core tenet of this criticism is that hiding code does not remove vulnerabilities; it merely makes them harder for legitimate researchers to find and report. In the open-source ecosystem, major vulnerabilities such as Heartbleed (OpenSSL) and Log4Shell (Log4j) were eventually discovered and mitigated because the code was accessible for public scrutiny. By moving behind a proprietary wall, Cal.com assumes the sole responsibility for security auditing, losing the benefit of the global developer community’s collective oversight.
Conversely, some industry analysts suggest that Cal.com’s move is a pragmatic response to the "asymmetric warfare" of modern cyber defense. While open-source maintainers often struggle with limited resources and volunteer time, malicious actors can now leverage high-powered AI to scan thousands of repositories simultaneously. This creates a scenario where the "bad actors" have a technological edge in discovery that traditional open-source workflows cannot match. The Linux kernel community has attempted to address this by integrating AI into their own defensive strategies. Greg Kroah-Hartman, a lead maintainer for the Linux stable branch, has reportedly been utilizing AI-assisted fuzzing techniques—internally referred to as the "clanker" branch—to proactively identify and fix bugs before they can be exploited. However, for a smaller organization like Cal.com, maintaining such a rigorous AI-driven defensive posture while keeping the code public may have been financially and operationally unsustainable.
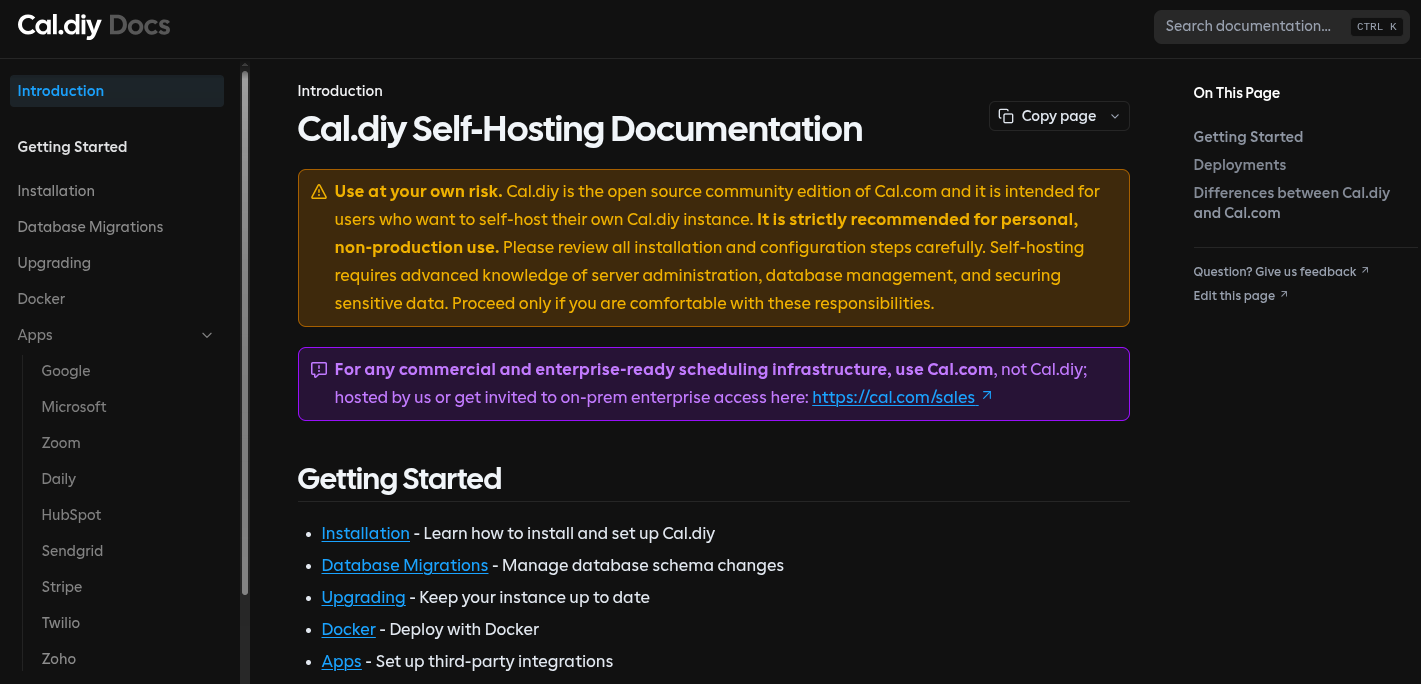
Beyond the security justifications, the shift also carries significant implications for the company’s commercial strategy. In tandem with the closed-source announcement, Cal.com introduced "Cal.diy," a new community-oriented version of the software. Licensed under the MIT License, Cal.diy is designed for individual self-hosters and hobbyists. However, it is explicitly stripped of the enterprise features that define Cal.com’s commercial value proposition. Absent from Cal.diy are essential tools for large-scale operations, such as Team management, Organization hierarchies, SAML-based Single Sign-On (SSO), SCIM directory synchronization, automated workflows, and advanced routing forms. The documentation for Cal.diy includes frequent disclaimers recommending it strictly for personal, non-production use, and it carries no official support or guarantees from the parent company.

This tiered approach suggests that while AI security was the catalyst, the transition also serves to protect Cal.com’s intellectual property and revenue streams. By restricting the most valuable "scheduling infrastructure" features to a closed-source, paid product, the company effectively prevents third-party competitors from "forking" their code to offer a rival managed service—a common challenge for open-source companies, often referred to as the "Amazon problem" or "cloud leaching." This pattern of moving from open-source to more restrictive licenses (such as the Business Source License or total closure) has been observed in other major tech players like HashiCorp, Redis, and MongoDB, who have all navigated the difficult balance between community contribution and corporate profitability.
The timeline of Cal.com’s evolution reflects the broader lifecycle of many "Open Core" startups. Founded in 2019, the project quickly gained traction by positioning itself as the ethical, transparent alternative to the proprietary status quo. It successfully raised millions in venture capital, buoyed by its high GitHub star count and active contributor base. However, as the company moved toward monetization and enterprise acquisition, the friction between open-source ideals and the requirements of a high-security SaaS product became evident. The divergence of the codebase in 2023 was the first major sign of this friction, leading directly to the current closure in 2024.
Looking forward, the implications for the open-source community are profound. If one of the most successful open-source SaaS companies of the last five years deems the model "too dangerous" due to AI, it may signal a chilling effect for new startups. Developers may be less inclined to share their core logic if they fear that an LLM will be used to dismantle their security within hours of a release. Furthermore, the reliance on AI as a justification for closing source code could set a precedent for other companies looking to exit the open-source ecosystem for commercial reasons, using "security" as a convenient and difficult-to-disprove rationale.
In the immediate term, existing Cal.com self-hosters who rely on enterprise features are faced with a difficult choice: migrate to the limited Cal.diy version, pay for a commercial license, or seek out remaining open-source alternatives that have not yet followed Cal.com’s lead. The company has stated that it will continue to support its current enterprise clients through the transition, but the days of a free, feature-complete, and auditable scheduling platform from Cal.com have officially come to an end.
As the technology sector continues to grapple with the dual-use nature of artificial intelligence, the Cal.com case study serves as a critical data point. It highlights a growing belief among software executives that the transparency which once defined the internet’s most robust systems may now be a liability. Whether this leads to a "Great Closing" of the software commons or inspires a new generation of AI-native open-source security tools remains to be seen. For now, Cal.com stands as a prominent example of a company choosing the fortress of proprietary development over the open plains of community collaboration, citing the unpredictable winds of the AI revolution as its primary motivator.