What is attack surface vs threat surface? This exploration dives into the crucial concepts of attack surface and threat surface, providing a clear understanding of their differences and the implications for organizational security. We’ll examine their components, impacts, and strategies for mitigation.
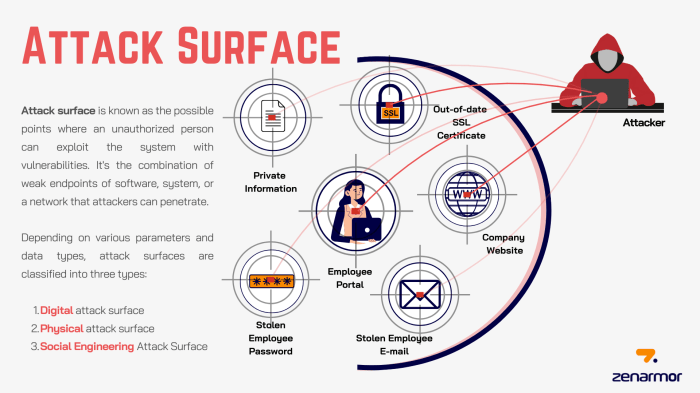
An attack surface represents the potential entry points for malicious actors to exploit vulnerabilities in a system. Conversely, the threat surface encompasses the actual threats targeting an organization. Knowing these nuances is critical for robust security planning.
Defining Attack Surface and Threat Surface
Understanding the difference between attack surface and threat surface is crucial for robust cybersecurity. These concepts, while related, represent distinct aspects of an organization’s vulnerability to cyberattacks. An accurate assessment of both is essential for developing effective security strategies.
Defining Attack Surface
The attack surface encompasses all potential entry points into a system or network. It’s essentially a catalog of everything that can be exploited by a malicious actor. This includes software applications, network protocols, hardware devices, and configurations. Essentially, it represents the entire set of accessible assets. Consider an online banking platform.
The attack surface would include the web application itself, the database servers, the network infrastructure, and even the operating systems of the servers.
Defining Threat Surface
The threat surface, conversely, focuses on the specific vulnerabilities in the attack surface that aparticular* threat actor is capable of exploiting. It’s a subset of the attack surface, tailored to the specific capabilities and intentions of the threat. This means a sophisticated nation-state attacker might target different aspects of the attack surface than a script kiddie. In our banking example, a nation-state actor might focus on the database’s security protocols, while a script kiddie might try to exploit known vulnerabilities in the web application’s login form.
Relationship Between Attack Surface and Threat Surface
The threat surface is entirely dependent on the attack surface. Without a defined attack surface, there’s no threat surface. However, the threat surface is also contingent on the threat actor. A specific attacker’s capabilities and intent define which components of the attack surface they’re likely to target.
Comparing and Contrasting Attack Surface and Threat Surface
| Characteristic | Attack Surface | Threat Surface |
|---|---|---|
| Definition | All potential entry points into a system or network. | Specific vulnerabilities in the attack surface that a particular threat actor can exploit. |
| Components | Software applications, network protocols, hardware devices, configurations, and more. | Vulnerable components of the attack surface, tailored to the threat actor’s capabilities and intent. |
| Scope | Broader, encompassing all potential points of access. | Narrower, focused on the specific vulnerabilities within the attack surface that a threat actor can leverage. |
Components of Attack Surface: What Is Attack Surface Vs Threat Surface
Understanding the attack surface is crucial for effective cybersecurity. It’s not just about identifying potential vulnerabilities; it’s about understanding where attackers might gain entry and how they might exploit those weaknesses. This section delves into the key components that make up an organization’s attack surface, exploring various attack vectors and providing real-world examples across different systems.The attack surface encompasses all potential points of entry for malicious actors seeking to compromise a system or network.
Identifying and mitigating vulnerabilities within these components is vital for robust security posture. A well-defined attack surface allows organizations to focus their security efforts on the most critical areas, prioritizing defenses and reducing the overall risk of compromise.
Key Components of an Attack Surface
The attack surface isn’t a monolithic entity; it’s composed of interconnected elements that must be assessed holistically. These components include software applications, network infrastructure, and human elements. Understanding each component is crucial to building a comprehensive defense strategy.
Understanding the difference between attack surface and threat surface is key in cybersecurity. Essentially, your attack surface is everything that could potentially be exploited, while the threat surface is a subset focused on the actual vulnerabilities actively targeted by attackers. This concept is fascinating when you consider the recent news about Blue Origin’s New Shepard astronauts getting priority access to the New Glenn ticket lottery here.
Thinking about who has access to what, and how that access might be exploited, helps highlight the critical importance of properly defining both attack and threat surfaces.
- Software Applications: This category encompasses all software running on a system, including web applications, databases, and internal tools. These applications often contain vulnerabilities that attackers can exploit to gain unauthorized access or execute malicious code.
- Network Infrastructure: The network architecture, including routers, firewalls, and servers, is a significant component of the attack surface. Vulnerabilities in network configurations or misconfigurations can allow attackers to penetrate the network and move laterally.
- Operating Systems: Operating systems (OS) are the foundation upon which applications and services run. Security flaws in the OS itself can provide entry points for attackers, leading to system compromise.
- Human Element: Human error, social engineering, and phishing attacks are often overlooked but represent a critical component of the attack surface. Employees can unintentionally introduce vulnerabilities through weak passwords, clicking malicious links, or divulging sensitive information.
- External Systems: External systems such as cloud services, third-party APIs, and connected devices expand the attack surface. Security issues in these external components can affect the entire system.
Types of Attack Vectors
Attack vectors are the specific pathways attackers use to exploit vulnerabilities within the attack surface. Understanding the various attack vectors is essential to develop effective mitigation strategies.
- Network-based Attacks: These attacks target network infrastructure, exploiting vulnerabilities in firewalls, routers, and other network devices. Denial-of-service (DoS) attacks and man-in-the-middle (MitM) attacks are common examples.
- Application-based Attacks: These attacks target vulnerabilities within software applications, such as SQL injection, cross-site scripting (XSS), and cross-site request forgery (CSRF). These attacks often exploit weaknesses in input validation and data handling.
- Social Engineering Attacks: These attacks exploit human psychology to manipulate individuals into revealing sensitive information or performing actions that compromise security. Phishing, baiting, and quid pro quo attacks are examples.
- Physical Attacks: These attacks involve physical access to systems or infrastructure. Theft of hardware, unauthorized access to facilities, and damage to equipment are examples.
Examples of Attack Surface Components Across Systems
The attack surface varies significantly depending on the system. Consider these examples:
- Web Applications: Web applications are vulnerable to various attacks like SQL injection, cross-site scripting (XSS), and insecure direct object referencing (IDOR). The attack surface includes the application’s code, database interactions, and user interfaces.
- Networks: Network components like routers, switches, and firewalls have configuration vulnerabilities that attackers can exploit. Weak passwords, outdated firmware, and inadequate security protocols create entry points.
- Mobile Devices: Mobile devices, especially those connected to corporate networks, present a unique attack surface. Malicious apps, insecure Wi-Fi connections, and lack of device security measures contribute to vulnerabilities.
Attack Surface Components and Vulnerabilities
This table illustrates some common attack surface components and potential vulnerabilities, along with mitigation strategies.
| Component | Description | Vulnerability Examples | Mitigation Strategies |
|---|---|---|---|
| Web Application | Software applications accessible over the internet | SQL injection, Cross-Site Scripting (XSS), Broken Authentication | Input validation, parameterized queries, secure coding practices, regular security audits |
| Network Infrastructure | Routers, switches, firewalls, and other network devices | Misconfigured firewalls, outdated firmware, default passwords | Regular security updates, strong passwords, access controls, network segmentation |
| Operating Systems | Underlying software controlling the system | Known vulnerabilities, privilege escalation, insecure configurations | Regular OS updates, security patches, access control lists, strong authentication |
| Human Element | Employees and users | Phishing, social engineering, weak passwords | Security awareness training, strong password policies, multi-factor authentication |
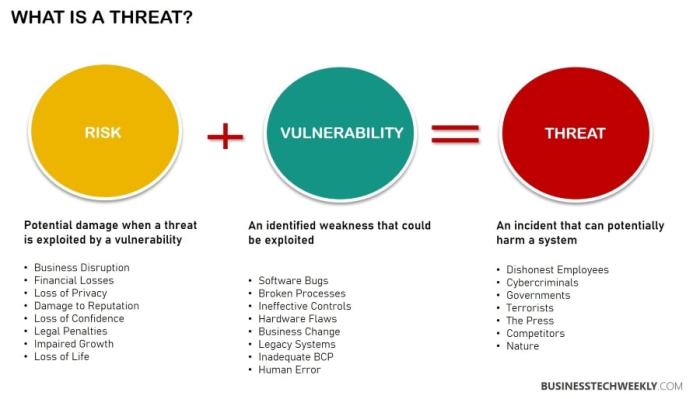
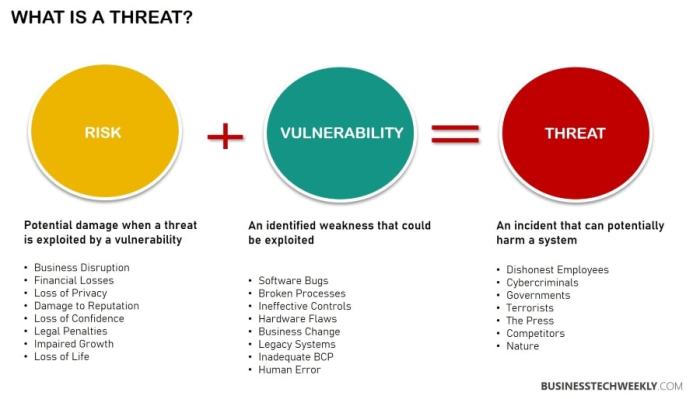
Components of Threat Surface
Understanding the threat surface is crucial for proactively identifying and mitigating vulnerabilities. It’s not just about the software or hardware; it encompasses the entire spectrum of potential entry points for malicious actors. This involves considering the interconnectedness of various systems and the diverse motivations driving threat actors.The threat surface encompasses far more than just a system’s digital footprint.
It considers the potential weaknesses in every facet of an organization, from physical access to human error. This comprehensive view allows for a more holistic approach to security, enabling organizations to better anticipate and respond to evolving threats.
Key Components of a Threat Surface
The threat surface is comprised of numerous interconnected components. These include vulnerabilities in physical access controls, logical access points, and the human element. A thorough understanding of these components is essential for effective security measures.
- Physical Components: Physical access points, such as doors, windows, and unsecured network equipment, can provide entry points for unauthorized individuals. Security measures like surveillance systems, security guards, and robust access control systems are essential to mitigate these risks. Examples include poorly secured warehouses, unattended vehicles with sensitive data, and unsecured server rooms.
- Logical Components: Logical components encompass network infrastructure, software applications, and data storage systems. Vulnerabilities in these areas can be exploited remotely, leading to data breaches, system disruptions, and unauthorized access. Examples include unpatched software, weak passwords, and poorly configured firewalls.
- Human Components: Human error, social engineering, and insider threats are significant factors within the threat surface. Phishing attempts, malware infections, and negligent data handling are examples of how human actions can lead to security breaches. Training and awareness programs are vital in mitigating these vulnerabilities. Examples include employees clicking on malicious links, failing to follow security protocols, or inadvertently sharing sensitive information.
Understanding the difference between attack surface and threat surface is crucial, but sometimes the complexities of modern technology make it hard to keep track of everything. For example, if you’re looking to reserve a Tesla Model 3, this resource can help you navigate the online reservation process. Ultimately, a secure online reservation system is a small part of a much larger threat surface that needs to be carefully considered.
So, next time you’re thinking about security, remember the difference between these two important concepts.
Types of Threat Actors
Understanding the motivations of different threat actors is critical for developing targeted security strategies. Threat actors range from opportunistic individuals to sophisticated state-sponsored groups.
- Opportunistic Actors: These actors often exploit easily accessible vulnerabilities, driven by financial gain or personal satisfaction. They may be individuals with limited technical skills but can still cause significant damage. Their motivations include financial gain, data theft, or malicious intent.
- Targeted Actors: These actors have specific goals, such as stealing intellectual property, disrupting operations, or gaining access to sensitive data. They often possess advanced technical skills and are motivated by financial gain, espionage, or political motivations. They might target specific companies or individuals.
- State-Sponsored Actors: These actors are often backed by governments and operate with significant resources and advanced capabilities. Their motivations include espionage, political influence, or economic disruption. They are highly organized and capable of sophisticated attacks.
Threat Surface Components, Motivations, and Potential Impact
The table below illustrates the interplay between different threat surface components, their potential motivations, and the potential impact of successful exploitation.
| Component | Description | Motivations | Potential Impact |
|---|---|---|---|
| Insider Threat | Employees or contractors with authorized access who misuse their privileges. | Financial gain, revenge, sabotage, or ideological motivations. | Data breaches, system disruptions, reputational damage, financial losses, and legal liabilities. |
| Phishing Attacks | Deceptive communications designed to trick individuals into revealing sensitive information. | Financial gain, espionage, or disruption. | Data breaches, identity theft, financial losses, and reputational damage. |
| Malware Infections | Malicious software designed to compromise systems and gain unauthorized access. | Financial gain, espionage, disruption, or political motivations. | Data breaches, system disruptions, financial losses, and reputational damage. |
| Unpatched Software | Software lacking security updates that can exploit known vulnerabilities. | Exploitation of known vulnerabilities. | Data breaches, system compromise, and significant damage to systems. |
Impact of Attack Surface and Threat Surface on Organizations
Understanding the attack surface and threat surface is crucial for any organization seeking to bolster its cybersecurity posture. A thorough comprehension of these surfaces, and their interrelationship, allows for a more proactive and effective approach to vulnerability management. Knowing the size and nature of these surfaces helps in prioritizing resources and implementing strategies that address the most critical risks.A large attack surface, coupled with a high threat surface, exponentially increases the potential for successful cyberattacks.
This is due to the increased number of potential entry points and the amplified likelihood of malicious actors exploiting these vulnerabilities. The impact of these surfaces on organizational security is not simply theoretical; it translates directly into financial losses, reputational damage, and operational disruptions.
Impact of a Large Attack Surface
A large attack surface presents a multitude of potential entry points for malicious actors. This increased exposure to cyber threats makes organizations more vulnerable to various attack vectors, from phishing scams to sophisticated exploits. The more avenues attackers have to penetrate, the higher the risk of compromise. This increased vulnerability translates into higher operational costs for incident response and remediation.
Furthermore, a large attack surface can hinder a company’s ability to quickly adapt to emerging threats, as the sheer volume of potential vulnerabilities can overwhelm security teams. A well-defined and manageable attack surface is essential for effective defense.
Impact of a Large Threat Surface
A large threat surface signifies a significant increase in the number of active and potential threats targeting an organization. This elevated threat landscape involves various actors, ranging from state-sponsored attackers to opportunistic cybercriminals, each with different motives and capabilities. Organizations with a large threat surface face an elevated risk of targeted attacks, as the attackers have a wider selection of potential targets and vulnerabilities to exploit.
Furthermore, a high threat surface necessitates continuous monitoring and proactive threat intelligence gathering to identify and mitigate emerging risks effectively.
Misalignment Between Attack Surface and Threat Surface
Misalignment between the attack surface and threat surface can create significant vulnerabilities. For example, an organization might have a large attack surface but a low threat surface, suggesting that while many points of entry exist, few actors are actively targeting them. Conversely, a small attack surface but a high threat surface indicates that despite having limited entry points, the organization is facing a significant number of sophisticated threats.
This discrepancy can lead to a false sense of security, resulting in inadequate defensive measures against emerging threats. A thorough understanding of both surfaces and their dynamic relationship is essential for creating a robust security posture.
Comparison Table of Impact
| Attack Surface Size | Threat Surface Size | Security Impact |
|---|---|---|
| Large | High | Increased risk of successful cyberattacks, higher incident response costs, potential for significant financial and reputational damage, difficulty in adapting to emerging threats. |
| Large | Low | Increased potential attack vectors, but limited active threats, increased operational costs for vulnerability management, potentially inadequate threat intelligence gathering. |
| Small | High | Limited attack vectors, but significant and sophisticated threats, potential for targeted attacks, increased need for robust threat intelligence and proactive measures. |
| Small | Low | Lower overall risk profile, limited threat actors and attack vectors, reduced operational costs for vulnerability management. |
Methods for Reducing Attack Surface and Threat Surface
Reducing an organization’s attack and threat surfaces is a crucial aspect of modern cybersecurity. A smaller attack surface presents fewer potential entry points for malicious actors, while a smaller threat surface minimizes the impact of successful attacks. This proactive approach is essential to mitigating risk and protecting valuable assets.Effective security strategies involve a multifaceted approach, recognizing that reducing one surface can indirectly affect the other.
Understanding the interplay between attack and threat surfaces allows for more targeted and comprehensive security measures. This involves not only securing individual systems but also considering the overall network architecture and potential vulnerabilities within it.
Methods for Reducing the Attack Surface
Identifying and mitigating potential entry points is fundamental to minimizing the attack surface. This involves a deep dive into the organization’s digital footprint, encompassing all systems, applications, and network configurations. Regular vulnerability assessments and penetration testing are crucial tools in this process.
Understanding the difference between attack surface and threat surface is crucial for cybersecurity. Essentially, your attack surface is everything that could potentially be exploited, while your threat surface focuses on the actual vulnerabilities. This becomes especially relevant when considering the recent Lightgun Shooter Crisis VR Brigade 2 heads PSVR Aim Controller support here. By addressing the potential attack vectors, you are effectively reducing the threat surface, thereby fortifying your security posture.
- Application Hardening: Implementing secure coding practices during application development significantly reduces vulnerabilities. This involves rigorous code reviews, input validation, and the use of secure libraries. Properly configured web applications, for example, can significantly limit the attack surface by preventing common vulnerabilities like SQL injection and cross-site scripting (XSS).
- Removing Unused Services and Ports: Unnecessary services and open ports represent potential attack vectors. Regular audits of systems and applications help identify and eliminate these vulnerabilities. Disabling unused protocols, such as older versions of FTP, can also minimize the attack surface.
- Network Segmentation: Dividing the network into smaller, isolated segments limits the impact of a breach. This isolates critical systems and data, preventing an attacker from easily moving laterally across the network. Consider isolating sensitive systems like financial servers or customer databases to minimize the scope of a potential breach.
- Regular Security Updates and Patching: Applying security updates and patches promptly is crucial for addressing known vulnerabilities. Organizations should establish a clear and consistent patching schedule to mitigate vulnerabilities in software and operating systems.
Methods for Reducing the Threat Surface
Reducing the threat surface focuses on minimizing the damage caused by a successful attack. This is achieved by isolating sensitive data, implementing robust access controls, and creating strong incident response plans. Protecting critical assets and sensitive data is a core aspect of minimizing the threat surface.
- Data Loss Prevention (DLP): Implementing DLP systems can restrict the movement and copying of sensitive data, limiting the potential impact of a breach. This includes encryption and access control to prevent unauthorized access and exfiltration of sensitive information.
- Principle of Least Privilege: Granting users only the necessary access rights to perform their tasks reduces the potential damage from compromised accounts. This minimizes the impact of a successful attack by limiting the attacker’s access to sensitive data and resources.
- Strong Authentication and Authorization: Robust authentication and authorization mechanisms, such as multi-factor authentication (MFA), strengthen the defense against unauthorized access. Implementing strong passwords, using MFA, and regularly reviewing access rights all help minimize the threat surface.
- Regular Security Awareness Training: Educating employees about phishing attacks, social engineering tactics, and other security threats helps mitigate the risk of human error. This can prevent employees from falling victim to social engineering tactics or clicking on malicious links.
Examples of Security Controls Reducing Both Attack and Threat Surfaces
Certain security controls can simultaneously reduce both the attack and threat surfaces.
- Network Segmentation: Reduces the attack surface by isolating systems and limiting lateral movement. This also reduces the threat surface by containing the impact of a breach. If one segment is compromised, the attacker’s access is limited to that segment, preventing wider damage.
- Data Encryption: Encrypting data at rest and in transit makes it unreadable to unauthorized individuals, reducing the threat surface. This also reduces the attack surface by making stolen data useless.
Security Controls and Impact on Surfaces, What is attack surface vs threat surface
| Security Control | Impact on Attack Surface | Impact on Threat Surface |
|---|---|---|
| Network Segmentation | Reduces the number of potential entry points and limits lateral movement. | Contains the impact of a breach, reducing the potential damage from compromised systems. |
| Application Hardening | Reduces vulnerabilities in applications, preventing exploitation. | Minimizes the damage caused by exploited vulnerabilities. |
| Regular Patching | Addresses known vulnerabilities in software and operating systems. | Reduces the impact of exploits on vulnerable systems. |
| Strong Authentication | Reduces the risk of unauthorized access to systems. | Limits the access of compromised accounts to sensitive resources. |
| Data Loss Prevention (DLP) | Reduces the potential for sensitive data leakage. | Minimizes the impact of data breaches by restricting the movement of sensitive information. |
Illustrative Examples
Understanding the attack and threat surfaces is crucial for any organization. Real-world scenarios highlight how a large attack surface combined with a high threat surface can create a significant security vulnerability. These examples demonstrate the importance of proactive risk assessment and mitigation strategies.
Examples of a Large Attack Surface
A large attack surface means numerous potential entry points for malicious actors. This can be caused by a lack of security controls, outdated systems, or complex configurations.
- A web application with numerous poorly secured APIs, outdated libraries, and multiple entry points for unauthorized access. This application lacks robust authentication and authorization mechanisms, exposing sensitive data and functionalities to attackers. The lack of input validation also makes it susceptible to injection attacks, such as SQL injection and cross-site scripting (XSS). Multiple vulnerabilities exist within the web application, making it an attractive target for malicious actors.
- An organization with a sprawling network of interconnected devices, many of which are legacy systems with known vulnerabilities. This could include outdated operating systems, poorly configured firewalls, and a lack of regular patching. The sheer number of interconnected devices increases the potential for compromise, making it a large attack surface.
- A company with a complex and extensive cloud infrastructure lacking proper access controls and monitoring. The distributed nature of cloud resources makes managing and securing them challenging. A lack of security best practices and insufficient monitoring tools leaves significant vulnerabilities.
Examples of a High Threat Surface
A high threat surface indicates that the potential for exploitation by malicious actors is substantial. This could be due to active threats in the environment, high attacker motivation, or a lack of security awareness among employees.
- A company that is a frequent target of nation-state actors. Their sensitive data and operations are considered valuable by sophisticated adversaries. The attackers possess the resources and motivation to launch complex and targeted attacks.
- A company with employees who lack cybersecurity awareness training. This could lead to phishing attacks, social engineering tactics, or unintentional data breaches. Employees may inadvertently provide access to unauthorized individuals through compromised credentials or malicious links.
- A company operating in a high-risk industry (e.g., financial services, healthcare) where the potential for financial loss or reputational damage from a security breach is high. The attacker’s motivations are heightened, and a successful breach could have severe financial implications and reputational damage.
Illustrative Example of a Security Breach
A combination of a large attack surface and a high threat surface can lead to a security breach.
- A medium-sized software company, “TechSolutions,” has a large attack surface due to its legacy infrastructure, multiple web applications with insufficient security controls, and a lack of a robust vulnerability management program. The company’s customer database and financial data are frequently targeted by sophisticated cybercriminals. The high threat surface is exacerbated by a lack of employee training on phishing scams and poor password management practices.
The attackers leverage both known and zero-day vulnerabilities. A sophisticated phishing campaign successfully targets an employee who provides credentials for an account with elevated privileges. With these privileges, the attackers gain access to the internal network, exfiltrate sensitive customer data, and disrupt operations. The company suffers significant financial losses, reputational damage, and legal ramifications due to the breach.
Final Thoughts
In conclusion, understanding the interplay between attack surface and threat surface is paramount for effective cybersecurity. A well-defined strategy that proactively mitigates vulnerabilities within the attack surface, while concurrently assessing and responding to active threats within the threat surface, is essential to building a resilient security posture. The goal is to create a strong defense that effectively balances potential entry points against actual threats, ultimately safeguarding the organization.