Prisma Cloud product deep dive sca explores the intricacies of this comprehensive security platform. We’ll delve into its core functionality, key features, and benefits, offering a high-level architectural overview and a comparison with competitor products. This in-depth analysis covers security architecture considerations, practical implementation strategies, use cases, and the latest cloud security trends, along with a technical deep dive.
From vulnerability detection and remediation to securing cloud infrastructure, this analysis will help you understand Prisma Cloud’s capabilities and how it can enhance your organization’s security posture in today’s dynamic cloud environment.
Introduction to Prisma Cloud Product
Prisma Cloud is a cloud-native security platform designed to protect applications and data throughout their lifecycle. It leverages a comprehensive approach to security, spanning various stages from development to deployment and runtime. This detailed look at Prisma Cloud will explore its core functionality, key features, architecture, and key components. Understanding these aspects allows organizations to effectively utilize Prisma Cloud to bolster their security posture.Prisma Cloud’s core function is to provide a unified security platform for cloud-native applications.
This encompasses a wide range of security tasks, from identifying and mitigating vulnerabilities to enforcing security policies and monitoring runtime behavior. This unified approach allows for a holistic security strategy that’s crucial in today’s dynamic cloud environments.
Core Functionality
Prisma Cloud’s core functionality is based on the principle of securing the entire application lifecycle. This involves continuous monitoring, vulnerability scanning, and automated remediation across development, deployment, and runtime stages. It achieves this through a combination of powerful tools and automated processes, reducing manual intervention and enhancing overall security efficiency.
Key Features and Benefits
Prisma Cloud offers a suite of features designed to enhance security across the application lifecycle. These features include automated vulnerability scanning, runtime threat detection, and policy enforcement. These benefits translate into reduced attack surface, quicker incident response, and improved overall security posture.
- Automated Vulnerability Scanning: Prisma Cloud automatically scans code repositories, containers, and images for vulnerabilities, allowing teams to identify and remediate weaknesses proactively.
- Runtime Threat Detection: Prisma Cloud actively monitors applications in production, detecting and responding to threats in real-time. This allows for immediate containment and mitigation of threats.
- Policy Enforcement: Prisma Cloud enforces security policies across the application lifecycle, ensuring that all deployments adhere to defined security standards. This ensures compliance and reduces the risk of security breaches.
- Compliance and Governance: Prisma Cloud helps organizations maintain compliance with industry regulations and internal policies. This facilitates smoother audits and reduces the risk of non-compliance penalties.
Prisma Cloud Architecture
Prisma Cloud employs a layered architecture designed for scalability and efficiency. The architecture is built around a central management platform that integrates with various cloud environments and tools. This integration allows for seamless data flow and analysis across the entire security lifecycle.
- Centralized Management Platform: A central platform for managing policies, configurations, and security insights across the entire environment.
- Agent-Based Monitoring: Agents deployed within the infrastructure continuously monitor and report on application and infrastructure security status. This facilitates real-time threat detection and analysis.
- Cloud-Native Integration: Seamless integration with various cloud platforms (e.g., AWS, Azure, GCP) enables comprehensive security across the cloud environment.
Key Product Components and Roles
The following table Artikels the key product components of Prisma Cloud and their respective roles in the security process.
| Component | Role |
|---|---|
| Security Posture Management | Identifies and assesses vulnerabilities, misconfigurations, and policy violations across the application lifecycle. |
| Cloud Security Posture Management | Provides comprehensive security analysis of cloud infrastructure, enabling proactive remediation. |
| Runtime Security | Monitors application behavior in production, detecting and responding to threats in real-time. |
| Threat Intelligence | Provides real-time threat intelligence and threat hunting capabilities, enabling organizations to stay ahead of emerging threats. |
Deep Dive into Specific Features
Prisma Cloud offers a comprehensive suite of security features designed to protect applications and infrastructure across the cloud. This deep dive explores the core security posture management, vulnerability detection, and remediation capabilities, along with Prisma Cloud’s approach to application and cloud infrastructure security, and its automation features. Understanding these features allows organizations to proactively address security risks and build a robust cloud security strategy.
Security Posture Management
Prisma Cloud provides a centralized platform for managing the security posture of applications and infrastructure. It continuously monitors for compliance violations, misconfigurations, and other security risks across various cloud environments. This includes assessing adherence to industry best practices and regulatory requirements like PCI DSS, HIPAA, and GDPR. By identifying and addressing these vulnerabilities, Prisma Cloud helps organizations maintain a strong security posture and avoid potential breaches.
Vulnerability Detection and Remediation
Prisma Cloud employs advanced scanning techniques to detect vulnerabilities in applications, infrastructure, and dependencies. This includes static and dynamic analysis of code, container images, and configuration files. The platform also leverages a vast database of known vulnerabilities to quickly identify potential threats. Beyond detection, Prisma Cloud offers remediation guidance, providing clear steps to fix identified vulnerabilities. This proactive approach helps organizations reduce risk and enhance the security of their applications and infrastructure.
Application Security
Prisma Cloud safeguards applications throughout their lifecycle. It protects against various threats, including injection flaws, cross-site scripting (XSS), and insecure configurations. The platform supports a variety of development environments, including containerized applications and serverless functions. This comprehensive approach helps organizations ensure that their applications are secure and resistant to attacks.
Cloud Infrastructure and Service Security
Prisma Cloud’s cloud infrastructure security features provide comprehensive protection for virtual machines (VMs), networks, and other cloud resources. The platform continuously monitors for unauthorized access attempts, malicious activities, and compliance violations. It also provides detailed insights into resource utilization and potential security bottlenecks. This proactive approach ensures that cloud infrastructure remains secure and operational.
Automation of Security Tasks
Prisma Cloud automates many security tasks, such as vulnerability scanning, compliance checks, and incident response. This automation reduces the workload on security teams, enabling them to focus on more strategic initiatives. The platform’s integration capabilities also automate workflows across different security tools and platforms, ensuring seamless data flow and improved efficiency. Automated tasks lead to faster identification and resolution of security issues.
Comparison with Competitors
| Feature | Prisma Cloud | Competitor A | Competitor B |
|---|---|---|---|
| Vulnerability Scanning | Comprehensive scanning of code, containers, and configurations | Focus on container images and code | Limited scanning, primarily focused on cloud infrastructure |
| Security Posture Management | Centralized platform for managing security posture across multiple clouds | Separate tools for managing different cloud platforms | Limited posture management, relying on external tools |
| Automation | Automates many security tasks, such as vulnerability scanning and compliance checks | Limited automation capabilities | Focus on incident response automation |
Note: Competitor A and Competitor B are hypothetical examples. Specific competitor features and capabilities may vary.
Security Architecture Considerations: Prisma Cloud Product Deep Dive Sca
Cloud security is paramount. A robust security architecture is critical to protect sensitive data and applications deployed in cloud environments. Without proper safeguards, organizations risk data breaches, regulatory violations, and operational disruptions. This is where Prisma Cloud plays a crucial role. Its comprehensive approach to cloud security helps organizations build and maintain a secure foundation.Implementing Prisma Cloud effectively requires understanding the specific security needs of various cloud setups.
This includes tailoring security controls to match the unique configurations of AWS, Azure, and GCP deployments. A well-defined security architecture, coupled with a robust security posture, is essential for mitigating potential threats and maintaining business continuity.
Importance of a Robust Security Architecture
A robust security architecture in cloud environments is not just a good practice; it’s a necessity. It encompasses a layered approach to security, involving multiple controls and strategies to protect against various threats. This approach is crucial for minimizing risks and ensuring business continuity. Effective security architectures consider factors like access controls, threat detection, and incident response, and include detailed plans to address potential vulnerabilities and threats.
This layered approach helps create a strong defense in depth, ensuring multiple points of failure are in place.
Best Practices for Implementing Prisma Cloud in Various Cloud Setups
Implementing Prisma Cloud in different cloud platforms (AWS, Azure, GCP) requires careful consideration of specific configurations and best practices. Each cloud provider offers unique services and tools, and Prisma Cloud must integrate seamlessly with these to ensure effective security.
- AWS: Leveraging AWS native security services, such as IAM (Identity and Access Management), along with Prisma Cloud’s capabilities for vulnerability scanning and threat detection, is crucial for a comprehensive security posture. Prisma Cloud’s integration with AWS services enables real-time visibility into cloud infrastructure and application configurations, providing critical data for security assessments.
- Azure: Similar to AWS, Prisma Cloud’s integration with Azure’s security features is key. Leveraging Azure’s security features, like Azure Security Center, alongside Prisma Cloud’s advanced threat detection capabilities helps create a comprehensive defense strategy. This includes proactive threat hunting, which is essential for detecting and responding to threats.
- GCP: For GCP deployments, Prisma Cloud integrates with GCP’s security tools and services to provide a unified security platform. This approach allows for a unified view of the security posture across different GCP services and resources. The platform enables centralized management and analysis, providing a holistic approach to security in GCP.
Security Controls Offered by Prisma Cloud
Prisma Cloud offers a comprehensive suite of security controls, encompassing various aspects of cloud security. These controls work together to build a strong security posture.
- Vulnerability Scanning: Prisma Cloud proactively identifies and assesses vulnerabilities in cloud infrastructure and applications, providing actionable insights for remediation.
- Threat Detection and Response: Prisma Cloud continuously monitors for suspicious activities and threats, providing alerts and insights to enable timely response.
- Compliance and Policy Management: Prisma Cloud helps organizations ensure compliance with industry regulations and internal policies by providing automated compliance checks and policy enforcement.
- Data Security: Prisma Cloud helps protect sensitive data by implementing appropriate access controls and data loss prevention measures.
Security Best Practices for Different Cloud Deployments
This table Artikels security best practices for different cloud deployments. These practices help create a secure environment and reduce potential risks.
Diving deep into the Prisma Cloud product deep dive SCA session, I was particularly fascinated by the security implications of cloud deployments. This naturally leads to the intriguing new discoveries about potential liquid water on Mars, as detailed in this fascinating article mystery of hidden liquid water on mars takes intriguing new turn. The connection to cloud security is clear – safeguarding our digital assets requires a similar level of investigation and attention to detail, just like the search for water on another planet.
Ultimately, a strong Prisma Cloud SCA is key to preventing vulnerabilities in our cloud environments.
| Cloud Deployment | Security Best Practices |
|---|---|
| AWS | Utilize AWS IAM roles and policies, enable AWS CloudTrail logging, and leverage Prisma Cloud’s integration with AWS services. |
| Azure | Implement Azure role-based access control (RBAC), utilize Azure Security Center, and ensure Prisma Cloud integrates seamlessly with Azure services. |
| GCP | Leverage GCP Identity and Access Management (IAM), use GCP Security Command Center, and integrate Prisma Cloud with GCP’s security features. |
Practical Implementation Strategies
Getting Prisma Cloud up and running effectively requires a structured approach. This section details practical implementation strategies, covering setup, policy customization, integration, dashboard utilization, and examples across various organizational types. A well-planned implementation is key to maximizing Prisma Cloud’s benefits and ensuring a secure environment.
Setting Up a Prisma Cloud Environment
A successful Prisma Cloud deployment begins with meticulous setup. This involves choosing the appropriate cloud provider and configuration options. Consider the specific needs of your infrastructure and the scale of your operations. Properly configuring your environment allows Prisma Cloud to effectively monitor and secure your resources.
- Account Creation and Configuration: Begin by creating a Prisma Cloud account and configuring necessary settings. This includes selecting the desired cloud provider (AWS, Azure, GCP) and specifying the scope of monitoring. Carefully review and adjust default settings to align with your organization’s security posture.
- Resource Discovery and Mapping: Import or manually map your cloud resources to the Prisma Cloud platform. This crucial step ensures Prisma Cloud has visibility into your entire infrastructure. Thorough mapping is essential for accurate security analysis and policy enforcement.
- Policy Deployment and Validation: Deploy initial security policies to enforce baseline security controls. Regularly validate policies to ensure they align with your evolving security requirements. Test and refine policies to prevent unexpected disruptions to production systems.
Customizing Security Policies
Policies define the specific security controls that Prisma Cloud enforces. Adjusting these policies is essential for fine-tuning security measures. Consider the different types of policies and the options available for customization.
- Policy Types and Scope: Prisma Cloud offers various policy types, including network security policies, container security policies, and workload security policies. Understanding the nuances of each type is critical to tailoring policies for optimal protection. Define the scope of each policy to target specific resources or environments effectively.
- Customizing Rule Sets: Adjust pre-defined rules or create custom rules to tailor policies to your unique security requirements. This involves setting thresholds for alerts, defining acceptable behavior patterns, and specifying exceptions for legitimate activities. Customization is essential for achieving a balance between security and operational efficiency.
- Prioritizing Policy Enforcement: Policies can be prioritized to control the order in which they are applied. This is crucial for enforcing critical security controls first. Prioritization allows for a hierarchical approach to security, mitigating potential conflicts between policies.
Integrating with Existing Tools and Platforms
Integration with existing tools and platforms is vital for a seamless workflow. Consider how Prisma Cloud can work alongside your existing infrastructure and security tools.
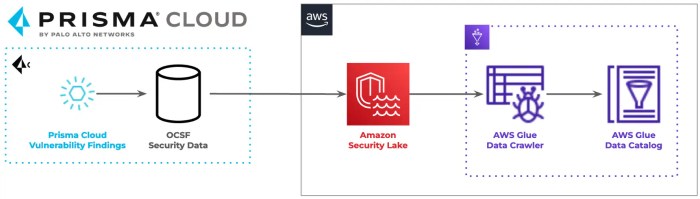
- API Integration: Use Prisma Cloud’s APIs to integrate with your existing CI/CD pipelines, security information and event management (SIEM) systems, and other tools. This ensures data flow and automates security tasks.
- Automation Tools: Leverage automation tools to automate the integration process. This simplifies configuration and reduces manual effort. Automated workflows can significantly improve efficiency.
- Data Synchronization: Configure data synchronization between Prisma Cloud and other platforms to ensure comprehensive visibility into security events. Streamlined data flow improves the accuracy and timeliness of security analysis.
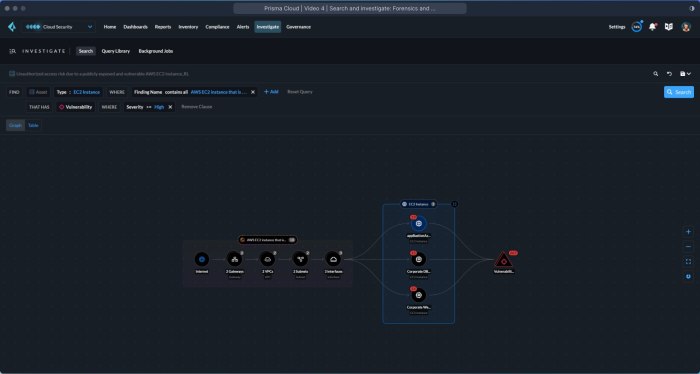
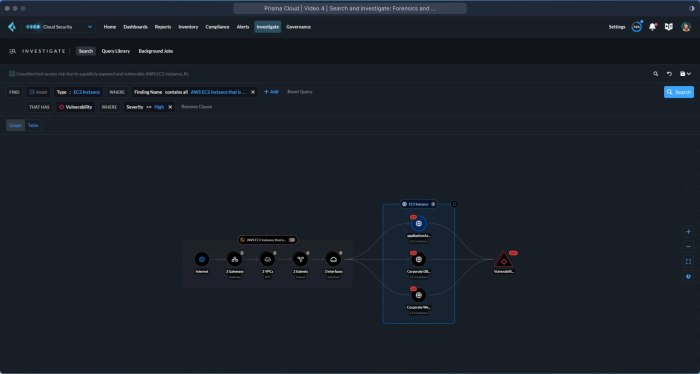
Using Prisma Cloud Dashboards and Reporting Tools
Prisma Cloud’s dashboards and reporting tools provide valuable insights into security posture and potential vulnerabilities. These tools are critical for understanding security trends and identifying areas needing improvement.
- Dashboard Features: Prisma Cloud dashboards provide a centralized view of security metrics, allowing for real-time monitoring of critical events. Key metrics include vulnerability detection, policy violations, and incident response status.
- Reporting Customization: Customize reports to generate detailed analyses of security events. This enables the identification of trends, root causes, and potential vulnerabilities. Customizable reports facilitate actionable insights and strategic decision-making.
- Actionable Insights: Extract actionable insights from generated reports. This data helps identify potential threats, prioritize remediation efforts, and improve overall security posture. Reports provide context for proactive security measures.
Implementing Prisma Cloud for Different Organization Types
Prisma Cloud’s flexibility allows for adaptation to various organizational needs. The approach to implementation should be tailored to specific business requirements and operational contexts.
- Start-ups: Start-ups benefit from Prisma Cloud’s ability to quickly secure evolving infrastructure and maintain a proactive security posture. Scalability and ease of use are paramount for their growth.
- Large Enterprises: Large enterprises can leverage Prisma Cloud’s robust features to secure complex and diverse environments. Integration with existing security systems and extensive reporting are crucial for their needs.
- Public Sector Organizations: Public sector organizations can utilize Prisma Cloud’s comprehensive security controls to meet compliance requirements and protect sensitive data. Regulatory compliance and data protection are essential concerns.
Prerequisites for Prisma Cloud Implementation
Successful Prisma Cloud implementation hinges on proper preparation. The prerequisites vary depending on the cloud environment.
| Cloud Environment | Prerequisites |
|---|---|
| AWS | AWS account credentials, IAM roles, access to relevant resources |
| Azure | Azure subscription credentials, resource access, and necessary roles |
| GCP | GCP project credentials, IAM roles, access to relevant resources |
Use Cases and Examples
Prisma Cloud isn’t just another security tool; it’s a practical solution for organizations facing the ever-evolving threat landscape. Its ability to proactively identify and mitigate vulnerabilities across various cloud environments makes it a valuable asset for modern enterprises. This section dives into real-world use cases, demonstrating how Prisma Cloud prevents breaches, ensures regulatory compliance, and enhances security posture in a multi-cloud world.
Real-World Use Cases of Prisma Cloud in Preventing Security Breaches
Prisma Cloud’s proactive threat detection and response capabilities are instrumental in preventing security breaches. It continuously monitors application traffic and infrastructure configurations for suspicious activities, providing early warnings about potential threats. This allows organizations to take swift action to mitigate risks before they escalate into major incidents. For instance, a financial institution using Prisma Cloud detected unusual access patterns to sensitive data, triggering an alert that enabled them to identify and block a potential insider threat, preventing a data breach.
How Prisma Cloud Helps Organizations Comply with Security Regulations
Many industries are subject to stringent security regulations, such as HIPAA, PCI DSS, and GDPR. Prisma Cloud plays a critical role in helping organizations meet these compliance requirements. By automating security audits, identifying vulnerabilities, and providing detailed reporting, Prisma Cloud simplifies the compliance process. This automated approach allows security teams to focus on strategic initiatives rather than being bogged down in repetitive compliance tasks.
A healthcare provider, for example, leveraged Prisma Cloud to ensure HIPAA compliance by automating the scanning and remediation of vulnerabilities in their cloud infrastructure.
How Prisma Cloud Improves Security Posture in a Multi-Cloud Environment
In today’s complex multi-cloud landscapes, maintaining a consistent security posture across various environments is challenging. Prisma Cloud provides a unified platform to manage security across different cloud providers and on-premises environments. This centralized approach streamlines security operations, enabling organizations to quickly identify and address security gaps across all their deployments. A large e-commerce company, using Prisma Cloud across AWS, Azure, and its on-premises data centers, significantly improved its overall security posture by having a single pane of glass for monitoring and management.
Practical Implementation Strategies for Prisma Cloud
Implementing Prisma Cloud effectively requires a strategic approach. A phased rollout, starting with key applications and infrastructure components, is often the most practical method. Detailed planning and communication with relevant teams are essential to ensure smooth integration and adoption. A detailed implementation strategy should address training, documentation, and ongoing maintenance. A well-defined strategy will ensure efficient use of resources and successful integration with existing security tools and workflows.
I’ve been diving deep into the Prisma Cloud product, specifically the SCA aspect, and it’s been pretty fascinating. However, my PS4 controller just stopped charging, so I’m taking a quick break to troubleshoot that issue. Hopefully, I can get it working again soon, and then I’ll be back to digging into the Prisma Cloud product’s deep security analysis.
You can find a helpful guide on what to do when your PS4 controller has stopped charging here. Once I’ve got that sorted, I’ll be back to exploring the Prisma Cloud SCA features.
Table of Prisma Cloud Use Cases
| Use Case | Description | Example Organization |
|---|---|---|
| Preventing Insider Threats | Detecting unusual access patterns and anomalies to prevent malicious insider activity. | Financial Institution |
| Meeting Security Regulations | Automating security audits and vulnerability scanning to ensure compliance with industry standards (e.g., HIPAA, PCI DSS). | Healthcare Provider |
| Improving Multi-Cloud Security | Providing a unified platform to manage security across different cloud providers and on-premises environments. | E-commerce Company |
| Enhanced Incident Response | Enabling quicker detection and response to security incidents through automated threat detection and incident correlation. | Software Development Company |
How Prisma Cloud Improves Security Incident Response
Prisma Cloud streamlines incident response by providing automated threat detection, incident correlation, and detailed reporting. This allows security teams to quickly identify, contain, and remediate security incidents. A software development company, using Prisma Cloud, experienced a significant reduction in incident response time after implementing the platform. This reduced downtime and minimized financial losses associated with security breaches.
Cloud Security Trends and Predictions
The cloud security landscape is constantly evolving, driven by the increasing adoption of cloud services and the ever-present threat of sophisticated attacks. Understanding current trends and anticipating future developments is crucial for organizations to proactively safeguard their cloud environments. Prisma Cloud, with its comprehensive approach to cloud security, plays a pivotal role in this dynamic environment.Predicting the future of cloud security involves analyzing existing threats, emerging technologies, and evolving attack vectors.
This analysis reveals key trends shaping the landscape and provides insights into how Prisma Cloud can adapt and evolve to address these challenges.
Current Trends in Cloud Security
The cloud security landscape is experiencing a rapid evolution, moving beyond basic perimeter defenses to encompass a broader spectrum of threats. Increased cloud adoption, coupled with the rise of serverless computing and containerization, has created new attack surfaces. The growing complexity of cloud environments demands sophisticated security tools and solutions. A key trend is the shift towards a more proactive and preventative security posture, focusing on threat detection and response before breaches occur.
I’ve been diving deep into the Prisma Cloud product, specifically the SCA aspect, lately. It’s fascinating how much security is packed into it, but sometimes, I find myself needing a quick distraction, like checking out the latest Amazon Fire TV Stick bundle with an Alexa Voice Remote and IR blaster. This Amazon Fire TV Stick bundle is a great way to unwind, and honestly, it made me think more about how crucial the Prisma Cloud’s SCA is in keeping my digital life safe.
Ultimately, though, I’m back to focusing on Prisma Cloud’s features, and how they’re helping me understand security threats.
This involves implementing advanced threat intelligence and automation to quickly identify and mitigate threats.
Future Developments and Innovations in Cloud Security
Future cloud security innovations will likely focus on enhancing automation, integrating AI and machine learning, and expanding security to encompass new cloud services and architectures. The increasing reliance on serverless computing and containerization requires new security strategies, which are evolving to address the unique challenges these architectures pose. This includes securing infrastructure-as-code deployments and the growing importance of securing data in transit and at rest within these environments.
Potential Future Directions of Cloud Security and Prisma Cloud’s Role
| Future Direction | Description | Prisma Cloud’s Role |
|---|---|---|
| AI-Powered Threat Detection and Response | Leveraging AI and machine learning to identify and respond to sophisticated threats in real time. | Enhance threat detection capabilities by integrating AI/ML models, automate incident response, and provide proactive threat hunting. |
| Zero Trust Security Models | Adopting a zero trust security model, verifying every user, device, and application accessing cloud resources. | Support and integrate with zero trust principles by providing comprehensive visibility and control across the cloud environment, enabling granular access controls. |
| Expanded Cloud Service Security | Extending security protections to new cloud services like serverless functions and edge computing. | Provide security coverage for emerging cloud services by extending its security posture to include these environments, and adapting to the evolving security needs of cloud services. |
| Multi-Cloud and Hybrid Cloud Security | Managing security across multiple cloud providers and on-premises environments. | Enable consistent security policies and controls across all environments by integrating with multiple cloud platforms and providing centralized management and visibility. |
Potential Evolution of Security Threats in the Cloud
Cloud security threats are evolving rapidly, with attackers becoming more sophisticated and employing new techniques. Sophisticated attacks targeting cloud infrastructure and applications will likely become more prevalent. The increasing use of automation in attacks, coupled with the growing volume of data breaches, requires a proactive approach to security. Ransomware attacks targeting cloud infrastructure, supply chain attacks, and the exploitation of vulnerabilities in cloud services are anticipated.
Furthermore, the rise of insider threats and the potential for misconfigurations within complex cloud environments will require robust security measures.
Role of Prisma Cloud in Mitigating Emerging Threats
Prisma Cloud plays a vital role in mitigating these emerging threats. Its proactive security posture, encompassing continuous monitoring and threat detection, allows organizations to quickly identify and respond to security incidents. Its integration with various cloud platforms and its comprehensive visibility into cloud resources enable a proactive approach to security, minimizing the impact of potential threats. Prisma Cloud can address the complex challenges posed by these evolving threats by providing a unified security platform.
By integrating advanced threat intelligence, automated response mechanisms, and comprehensive visibility, Prisma Cloud strengthens the security posture of organizations operating in the cloud.
Technical Deep Dive
Prisma Cloud’s efficacy hinges on its robust technical architecture, meticulously designed to detect and respond to threats in real-time. This section delves into the intricate mechanisms behind data collection, analysis, threat identification, and response, alongside a detailed overview of the underlying technologies and the Prisma Cloud API. We’ll also compare Prisma Cloud’s architecture with its competitors to highlight its unique strengths.Prisma Cloud’s technical capabilities are built upon a foundation of advanced data analysis techniques and a comprehensive understanding of modern threat landscapes.
This allows for rapid identification and response to security breaches, minimizing potential damage.
Data Collection and Analysis Mechanisms
Prisma Cloud utilizes a multifaceted approach to data collection, encompassing various sources within the cloud infrastructure. These sources include logs, configuration files, network traffic, and application activity. This data is then aggregated and processed using sophisticated algorithms and machine learning models to identify anomalies and potential threats. The collected data is securely stored and analyzed to generate insights into security posture.
Data normalization and standardization are crucial steps to ensure accuracy and consistency in threat detection.
Threat Identification and Response
Prisma Cloud employs a combination of signature-based and anomaly-based detection methods. Signature-based detection relies on pre-defined patterns of malicious activity, while anomaly-based detection identifies deviations from expected behavior, potentially signaling new or evolving threats. This dual approach significantly enhances the system’s ability to detect both known and unknown threats. In real-time, Prisma Cloud correlates these detections, leveraging threat intelligence feeds to provide immediate alerts and recommendations for mitigation.
Underlying Technologies
Prisma Cloud leverages a variety of technologies, including advanced machine learning algorithms, graph databases, and distributed computing frameworks. These technologies enable the platform to process vast amounts of data efficiently and identify subtle patterns indicative of malicious activity. For example, graph databases facilitate the correlation of disparate security events, revealing the interconnectedness of threats.
Prisma Cloud API, Prisma cloud product deep dive sca
The Prisma Cloud API provides a robust interface for integrating Prisma Cloud into existing security workflows. It allows developers to automate security tasks, customize threat detection rules, and integrate with other security tools. This comprehensive API enables seamless automation of security operations and empowers users to integrate Prisma Cloud into their existing CI/CD pipelines.
Technical Architecture Comparison
| Feature | Prisma Cloud | Competitor A | Competitor B |
|---|---|---|---|
| Data Collection | Multi-source, including logs, network traffic, and application activity. | Primarily logs and network traffic. | Focus on agent-based data collection. |
| Threat Detection | Signature-based and anomaly-based, leveraging threat intelligence. | Primarily signature-based. | Stronger focus on behavioral analytics. |
| Scalability | Highly scalable, leveraging cloud-native architecture. | Scalable but potentially with limitations in certain scenarios. | Scalability depends on deployment configuration. |
| API | Comprehensive API for integration and automation. | Basic API for limited integration. | API with robust features for advanced automation. |
This table provides a simplified comparison; actual architecture details may vary based on specific deployments and features. Key differences often lie in the approach to data collection, the sophistication of threat detection algorithms, and the extensibility of the platform through APIs.
Final Conclusion
In conclusion, Prisma Cloud SCA offers a powerful solution for securing cloud environments. Its comprehensive features, practical implementation strategies, and real-world use cases demonstrate its potential to significantly enhance security posture and improve incident response. Understanding the evolving cloud security landscape and Prisma Cloud’s role in mitigating future threats is crucial for organizations looking to maintain a strong security stance.
The technical aspects, while complex, provide a clear picture of the technology underpinning Prisma Cloud’s effectiveness.