How Static Code Analysis Helps Reduce Software Bugs, and Money Spent!
The landscape of modern software development is fraught with complexities, none more pervasive and potentially costly than software bugs. While an inherent part of the development cycle, the financial and operational repercussions of undetected defects can be astronomical, particularly when these issues are discovered late in the software development lifecycle (SDLC) or, worse, post-launch. This article delves into the critical role of static code analysis (SCA) as a proactive measure to mitigate these risks, significantly reducing both the volume of software bugs and the substantial financial outlay associated with their remediation.
The Escalating Cost of Software Defects: A Global Concern
The financial burden imposed by poor software quality is staggering. According to a 2022 report by the Consortium for Information & Software Quality (CISQ), the cost of poor software quality to the US economy alone reached an alarming $2.41 trillion. This comprehensive figure encompasses a wide array of expenses, from application downtime and extensive debugging efforts to the insidious drain on productivity across organizations. Such statistics underscore the urgent need for more effective quality assurance mechanisms within the software industry.
Beyond general quality issues, security vulnerabilities, often stemming from software bugs, present a particularly acute financial threat. IBM’s Cost of a Data Breach Report 2025 highlights that the estimated average global cost of a data breach stands at a formidable $4.44 million. Many of these breaches are directly attributable to flaws in software, emphasizing the critical intersection of code quality and cybersecurity. These figures are not mere abstract statistics; they represent tangible losses, including direct financial damages, regulatory fines, legal fees, reputational harm, and long-term erosion of customer trust.
The principle is clear and well-documented: the later a bug is identified within the SDLC, the more expensive it becomes to fix. A seminal 2010 study from the IBM System Sciences Institute illustrated this escalation dramatically, revealing that a bug detected during the traditional testing phase could cost up to 15 times more to rectify than if it were found during the design stage. This cost multiplier further balloons to as much as 100 times if the defect manages to slip through to the maintenance or production phases. This exponential increase is due to several factors: increased complexity in isolating the root cause, potential ripple effects across interconnected systems, the need for emergency patches, and the deployment of extensive resources to mitigate production incidents.
The average cost of a bug, therefore, is not a fixed sum but a dynamic figure influenced by its detection point. These costs include not only the direct labor involved in debugging and re-coding but also the indirect expenses associated with project delays, missed market opportunities, negative customer experiences, and the potential for regulatory non-compliance leading to significant penalties.
Understanding Static Code Analysis: A Proactive Defense Mechanism
Static code analysis represents a fundamental shift in how organizations approach software quality and security. Unlike dynamic analysis, which involves executing code to identify issues, SCA examines source code, bytecode, or binary code without executing it. This non-execution approach allows for early detection of potential vulnerabilities, coding standard violations, performance bottlenecks, and other quality issues at the earliest possible stages of development.
The methodology behind SCA aligns perfectly with the "shift-left" paradigm in software development. This philosophy advocates for moving critical tasks, such as testing and quality assurance, to the left (earlier) in the development timeline. By integrating SCA into the initial stages of coding, developers receive immediate feedback on potential issues, allowing for prompt correction before the code is even compiled or integrated with other components. This stands in stark contrast to traditional methods where bugs might only surface during integration testing, quality assurance (QA), or even worse, after deployment to production environments.
The evolution of SCA tools has been significant, moving from basic linting utilities that checked for stylistic errors to sophisticated platforms capable of deep semantic analysis. Modern SCA tools can identify a wide array of issues, including:
- Security Vulnerabilities: Such as SQL injection, cross-site scripting (XSS), insecure deserialization, hardcoded credentials, and path traversal. These align closely with common vulnerabilities listed in frameworks like the OWASP Top 10.
- Memory Leaks: Unreleased memory that can lead to performance degradation and system crashes.
- Concurrency Issues: Race conditions and deadlocks in multi-threaded applications.
- Coding Standard Violations: Ensuring adherence to predefined coding guidelines and best practices, leading to more maintainable and readable code.
- Performance Bottlenecks: Inefficient algorithms or resource usage patterns.
- Potential Bugs: Null pointer dereferences, unhandled exceptions, logical errors.
SCA in Action: Lowering Risks and Liberating Teams
Implementing static code analysis transforms the development workflow, leading to tangible benefits that directly translate into cost savings:
-
Early Detection, Easier Fixes: The most significant advantage of SCA is its ability to flag issues as soon as the code is written. When a developer receives immediate feedback on a potential bug or vulnerability, the context of the code is fresh in their mind. This allows for rapid, often instantaneous, correction without the need for extensive debugging sessions or revisiting code written weeks or months prior. This "fix-it-now" approach drastically reduces the time and effort required for remediation compared to unraveling deeply embedded issues discovered much later.

-
Lower Production Risks: Undetected bugs, especially security vulnerabilities, pose immense risks in live production environments. A single security flaw can lead to data breaches, system outages, financial fraud, and significant reputational damage. SCA acts as a vital gatekeeper, identifying and preventing these issues from ever reaching production. By catching security flaws like default credentials or hardcoded tokens before deployment, organizations can avoid costly incident response efforts, potential regulatory fines (e.g., GDPR, HIPAA, PCI DSS), and the erosion of customer trust that accompanies such incidents.
-
Freeing Up Your Team: Manual code reviews, while valuable, are often time-consuming, prone to human error, and can become a bottleneck in fast-paced development cycles. SCA automates many repeatable checks, offloading the burden of identifying common errors and adherence to coding standards from developers and QA teams. This automation frees up highly skilled personnel to focus on more complex architectural challenges, innovative feature development, and intricate logical issues that require human ingenuity. The result is increased developer productivity, reduced backlog, and a more efficient allocation of human capital.
-
Repaying Technical Debt: Technical debt refers to the implied cost of future rework necessary to address suboptimal solutions chosen for expediency. Unchecked, technical debt can accumulate rapidly, making a codebase difficult to maintain, extend, and secure. SCA helps in actively managing and reducing technical debt by enforcing consistent code quality standards. By identifying non-compliant code, architectural smells, and potential refactoring opportunities, SCA ensures that the codebase remains clean, maintainable, and inexpensive to operate over its lifecycle. This proactive approach prevents the mental and financial burden associated with a sprawling, unmanageable legacy system.
Static Code Analysis in CI/CD Pipelines: The Ultimate Quality Gate
The true power and cost-saving potential of static code analysis are maximized when it is seamlessly integrated into Continuous Integration/Continuous Delivery (CI/CD) pipelines. In a CI/CD environment, every code commit or pull request triggers an automated build, test, and deployment process. Integrating SCA into this pipeline transforms it into a robust "quality gate," ensuring that no substandard or vulnerable code makes it into the main codebase.
When SCA is run on every commit or pull request, it automatically checks for a predefined set of issues, including security vulnerabilities highlighted by industry standards like OWASP. If the code fails to meet the specified quality and security thresholds—for instance, if it contains a critical vulnerability or violates a mandatory coding standard—the CI/CD pipeline can be configured to halt progress. The build fails, and the developer responsible is immediately notified, requiring them to fix the identified issues before the code can be merged into the main branch.
This mechanism fundamentally shifts quality assurance from a reactive, end-of-cycle activity to a proactive, continuous process. It eliminates the ability for identifiable bugs and security flaws to bypass checks, preventing them from propagating into the codebase where they would be significantly more expensive and complex to fix. This strict enforcement through quality gates is instrumental in reducing long-term technical debt, minimizing security risks, and ensuring the delivery of consistently high-quality software.
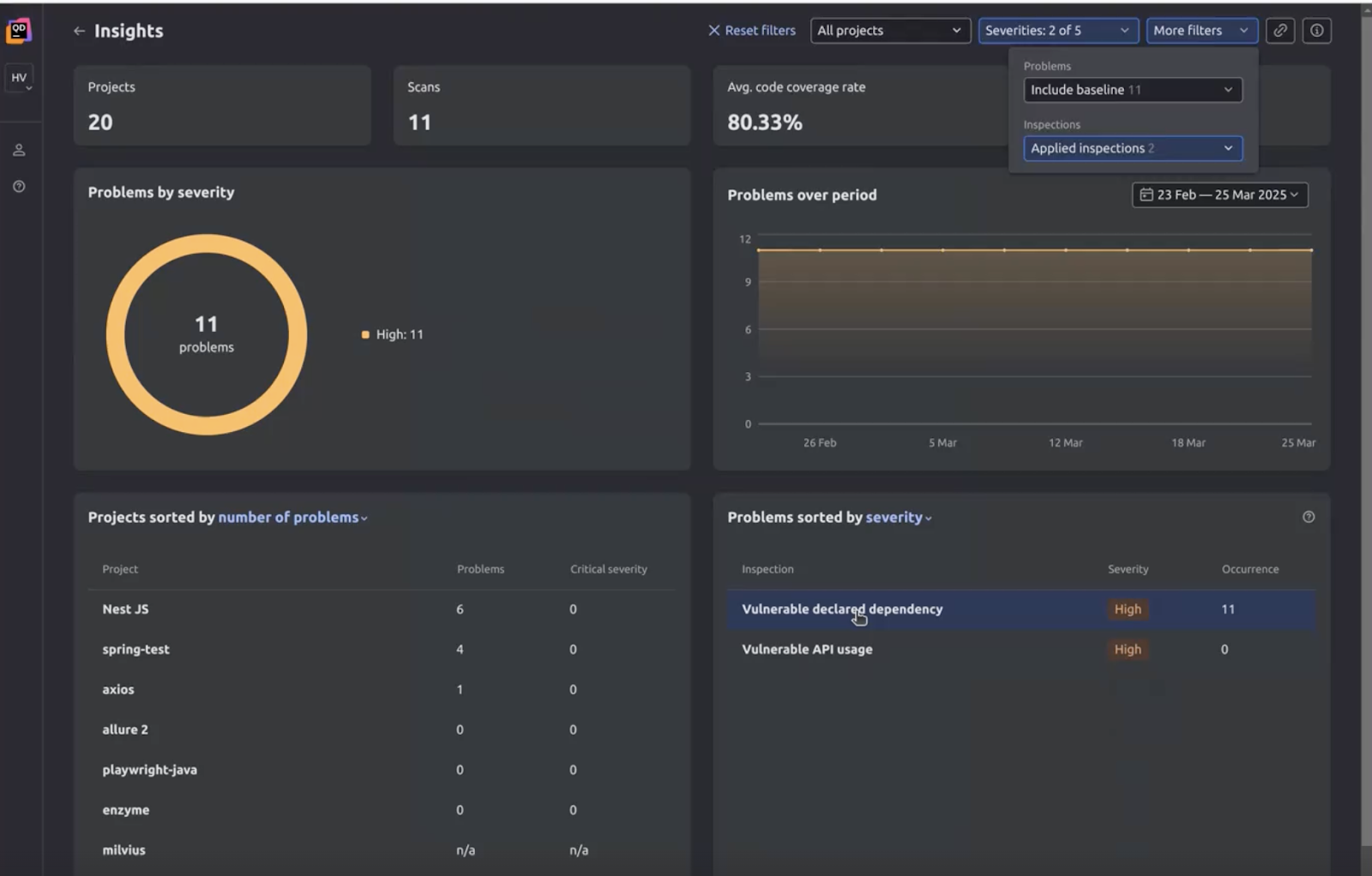
Qodana: A Real-World Solution for Bug Cost Control
JetBrains’ Qodana platform exemplifies how modern static code analysis tools can empower development teams to control bug costs effectively. Built on the robust and widely trusted linters of JetBrains’ Integrated Development Environments (IDEs), which have been utilized by over 18 million developers since 2001, Qodana offers a comprehensive solution for continuous code quality.
Qodana integrates smoothly into existing development environments and CI/CD workflows, providing real-time feedback, enforcing consistent code standards, and suggesting actionable fixes. Key capabilities include:
- Real-time Feedback: Developers receive immediate alerts on issues within their IDEs, allowing for instant correction.
- Customizable Quality Profiles: Teams can define and enforce specific coding standards and security policies tailored to their project requirements.
- Comprehensive Language Support: Covering a wide array of programming languages, ensuring broad applicability across diverse projects.
- Detailed Reports and Metrics: Providing insights into codebase health, technical debt trends, and compliance status.
- Integration with Existing Tools: Seamlessly working with popular version control systems, CI/CD platforms, and project management tools.
By leveraging Qodana, development teams can identify and rectify issues earlier, ensuring the delivery of secure, high-quality code without incurring the prohibitive costs associated with extensive refactoring, emergency patching, or system downtime.
Illustrative Scenario: Mitigating Hardcoded Secret Values
Consider a common scenario in which a code or configuration change inadvertently introduces a security weakness: the hardcoding of secret values, such as API keys or database credentials, directly into the source code.
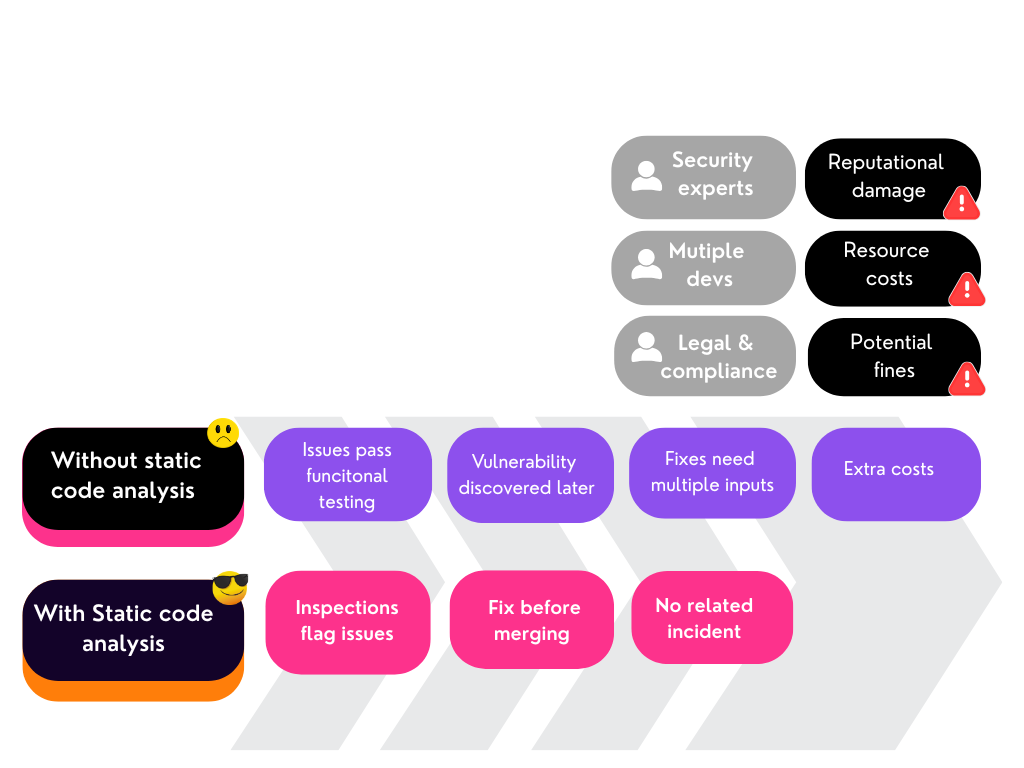
Without Static Code Analysis:
In the absence of SCA, this subtle yet critical vulnerability can easily escape detection during manual code reviews, which often focus on business logic rather than deep security scrutiny. It might also pass through functional testing, as the feature itself may work as intended. The vulnerability could then remain undiscovered until much later in the SDLC—perhaps during a dedicated security audit, a penetration test, or, most critically, after release when an attacker exploits it.
If this vulnerability reaches the shipped product, the consequences are severe:
- Unauthorized Access & Data Breaches: Attackers can gain control over systems, access sensitive data, or impersonate legitimate services.
- Reputational Damage: Loss of customer trust, negative publicity, and long-term harm to the brand.
- Financial Penalties: Regulatory fines (e.g., for data privacy violations), legal fees from class-action lawsuits, and costs associated with mandatory data breach notifications.
- Emergency Response Costs: Mobilization of incident response teams, forensic analysis, emergency patching, and communication efforts, all at a premium.
- Loss of Business: Customers might migrate to competitors, and partners might lose confidence.
The cost to fix the problem in a live environment escalates dramatically, requiring coordinated patches, rapid deployment cycles, and potentially service downtime, all of which are far more expensive than if the error had been detected during development.
With Static Code Analysis:
Integrating SCA into the development workflow fundamentally changes this outcome. At the point of code commit or pull request, the SCA tool automatically scans the changes. It immediately flags the hardcoded secret value as a critical security vulnerability and, crucially, can be configured to halt the CI/CD pipeline.
The developer responsible is instantly alerted to the specific issue, often with suggested fixes or direct links to remediation guidelines. Because the feedback is immediate and contextual, the developer can rectify the vulnerability in minutes, before the code is merged into the main branch. This proactive interception prevents the bug from ever becoming part of the wider codebase, eliminating all downstream risks and associated costs. The process ensures that security is an inherent priority from the outset, rather than a reactive expense, significantly reducing the likelihood of costly security incidents and compliance breaches.
Other critical security weaknesses SCA can catch include:
- Improper Input Validation: Leading to injection attacks (SQL, command).
- Broken Access Control: Allowing unauthorized users to perform actions.
- Insecure Configuration: Misconfigurations in servers, databases, or application components.
- Cross-Site Scripting (XSS): Injecting malicious scripts into web pages.
- Use of Components with Known Vulnerabilities: Identifying outdated libraries or frameworks with publicly disclosed weaknesses.
Beyond Bugs: Strategic Advantages for Sustainable Software Development
The benefits of static code analysis extend beyond mere bug reduction and cost savings, contributing to a more robust and sustainable software development ecosystem:
- Compliance and Governance: SCA tools assist organizations in meeting stringent regulatory requirements and industry standards (e.g., ISO 27001, SOC 2, HIPAA). By providing auditable proof of code quality and security checks, SCA simplifies compliance efforts and reduces audit risks.
- Developer Productivity and Morale: By catching common errors automatically, developers spend less time on tedious debugging and more time on creative problem-solving and feature development. This not only boosts productivity but also improves developer morale, fostering a more satisfying work environment.
- Enhanced Reputation and Customer Trust: Consistently delivering high-quality, secure software builds and maintains a strong reputation. In an era where data breaches are common, a proactive approach to security through SCA differentiates organizations and enhances customer trust.
- Knowledge Transfer and Onboarding: SCA tools enforce consistent coding styles and best practices, making it easier for new team members to understand and contribute to the codebase. This facilitates smoother onboarding and more effective knowledge transfer.
Conclusion
The undeniable value of static code analysis in modern software development cannot be overstated. It is an indispensable tool not only for drastically reducing the incidence and cost of software bugs but also for fostering a culture of quality, enhancing security posture, and achieving significant operational and financial efficiencies. By embracing a shift-left approach and integrating powerful SCA platforms like Qodana into their CI/CD pipelines, organizations can transform their development processes from reactive firefighting to proactive quality assurance. This strategic investment empowers teams to deliver secure, reliable, and high-performing software, safeguarding against financial losses and solidifying market leadership.
For teams looking to proactively reduce software bugs and control associated costs, exploring robust static code analysis solutions is a crucial next step.